We have released Cerbero Suite 6.4 and Cerbero Engine 3.4. What follows is a list of the most important new features.
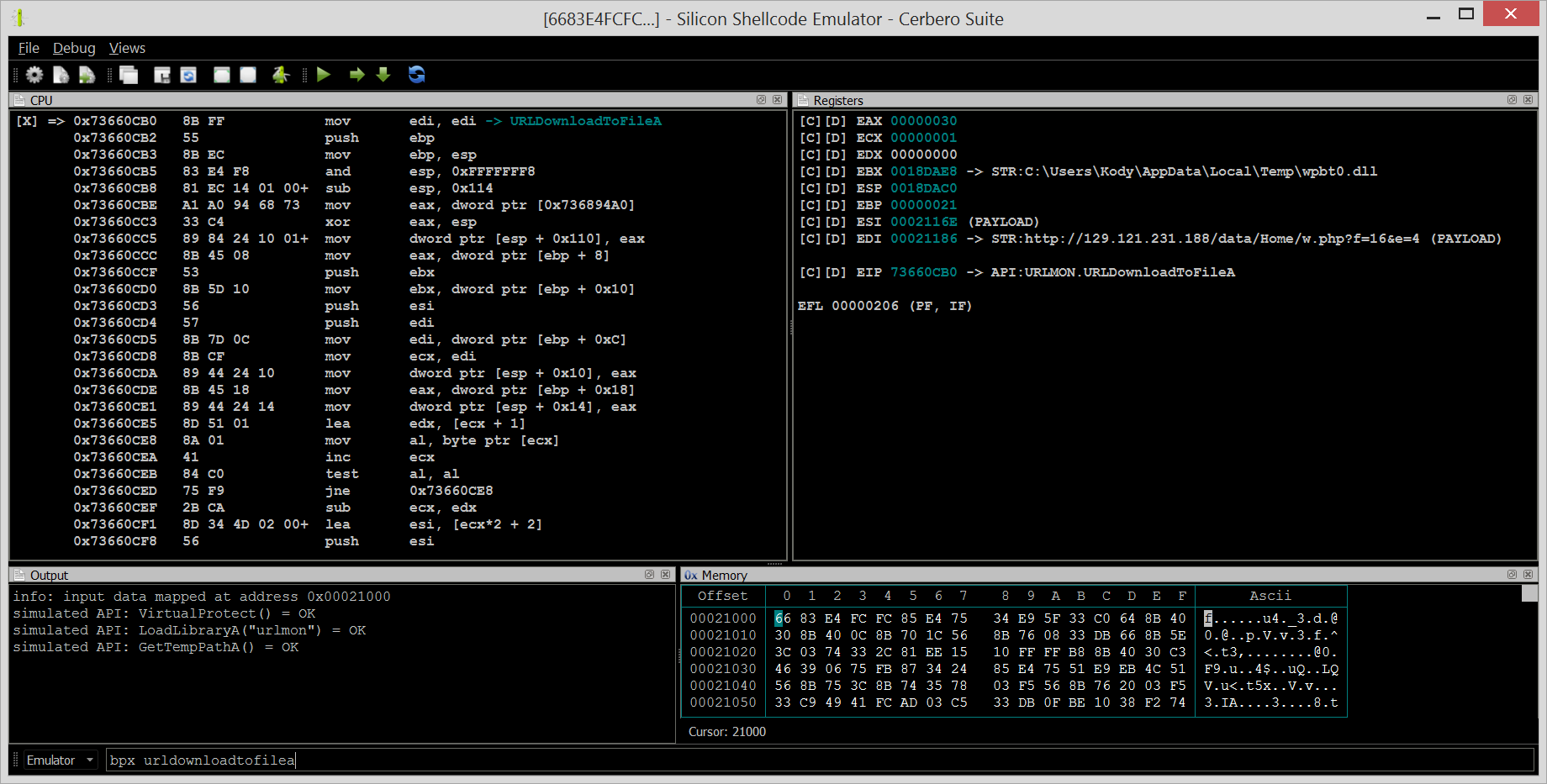
Silicon Shellcode Emulator
Silicon Shellcode Emulator is a lightweight x86/x64 emulator designed for Windows shellcode. The package is available to all commercial licenses of Cerbero Suite Advanced.
The emulator can be launched from the main window, from the command line or from an action.
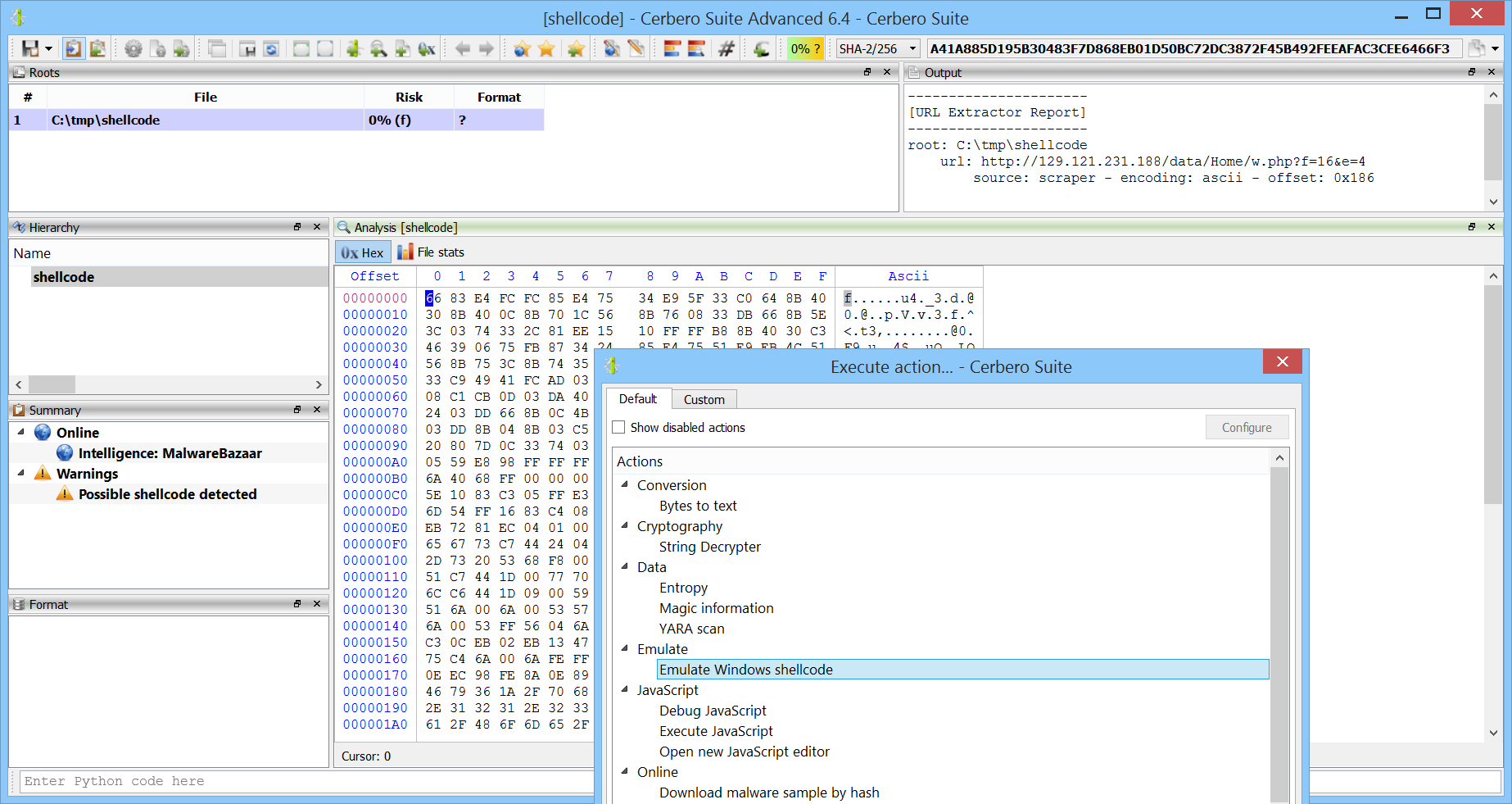
The emulator can be executed from an action within any hex view.
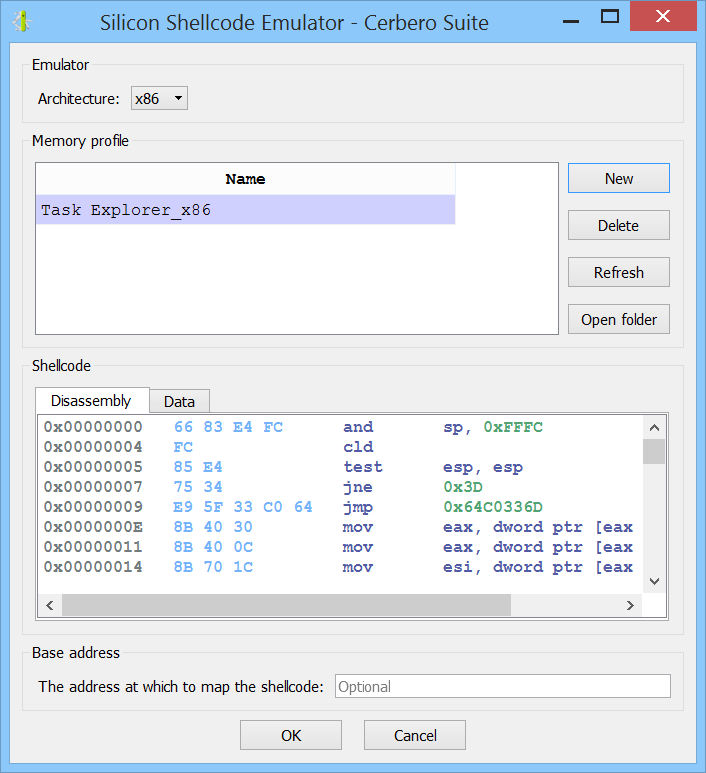
Before the emulator is launched, a settings dialog is shown: an architecture and a memory profile must be selected.
If a memory profile isn’t already available, on Windows you can create a new one from a process on your system. An x86 shellcode requires an x86 process memory profile and an x64 shellcode requires an x64 process memory profile. Make sure that the selected process maps Urlmon.dll, which is often used by shellcode. On Linux and Mac it is necessary to copy a memory profile created on Windows to the profile directory.
Once the profile has been selected, the emulator can be launched.
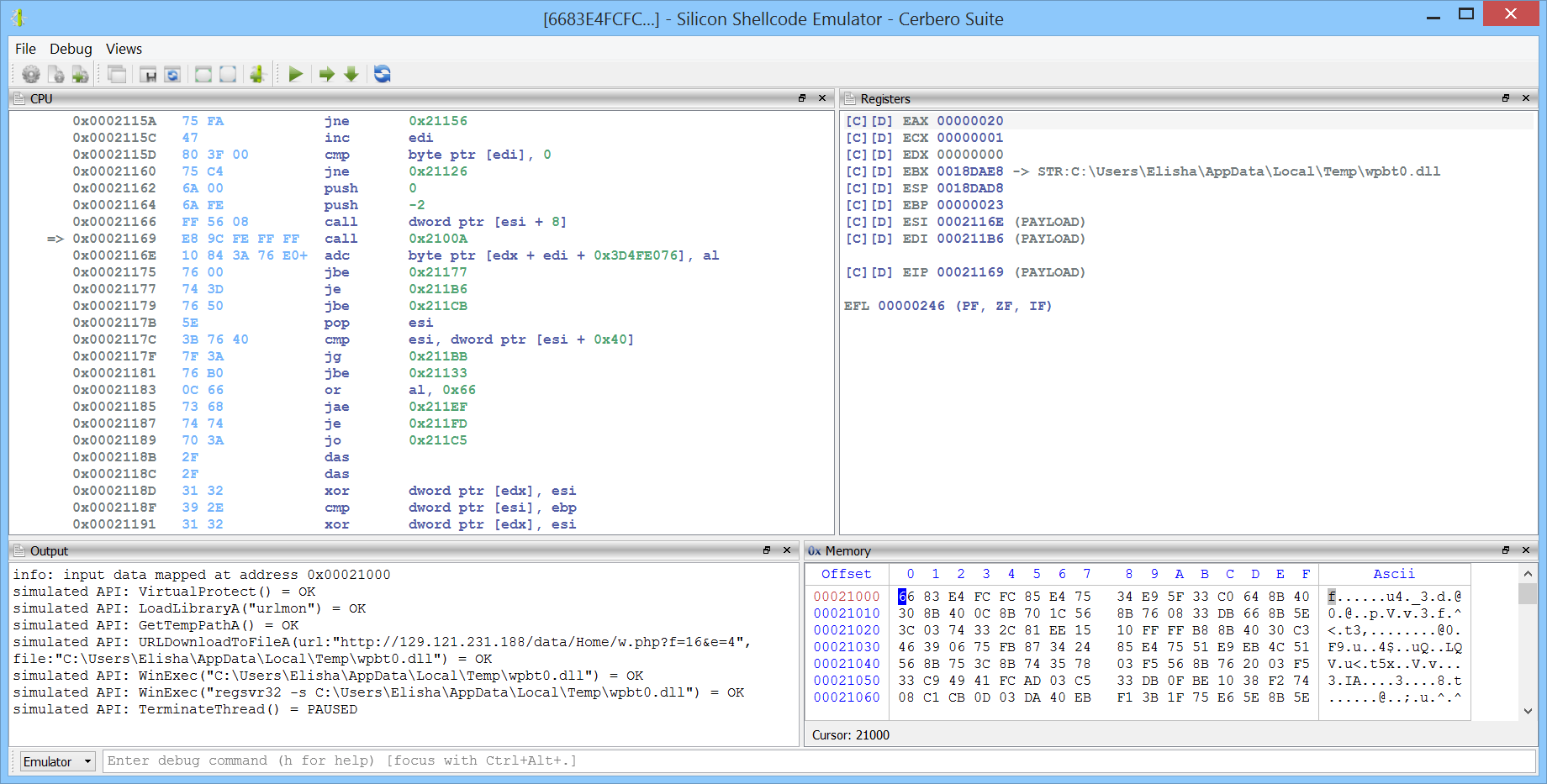
In this case, we didn’t step through the code manually and just let the emulator run the code. As can be observed in the output view, the emulator simulated the APIs invoked by the shellcode.
In the upcoming weeks we’ll be showcasing Silicon Shellcode Emulator in videos and articles.
IceDark Theme
To celebrate the release of Silicon Shellcode Emulator we have created a new theme which gives Cerbero Suite a look which might be familiar to old-school fellows.
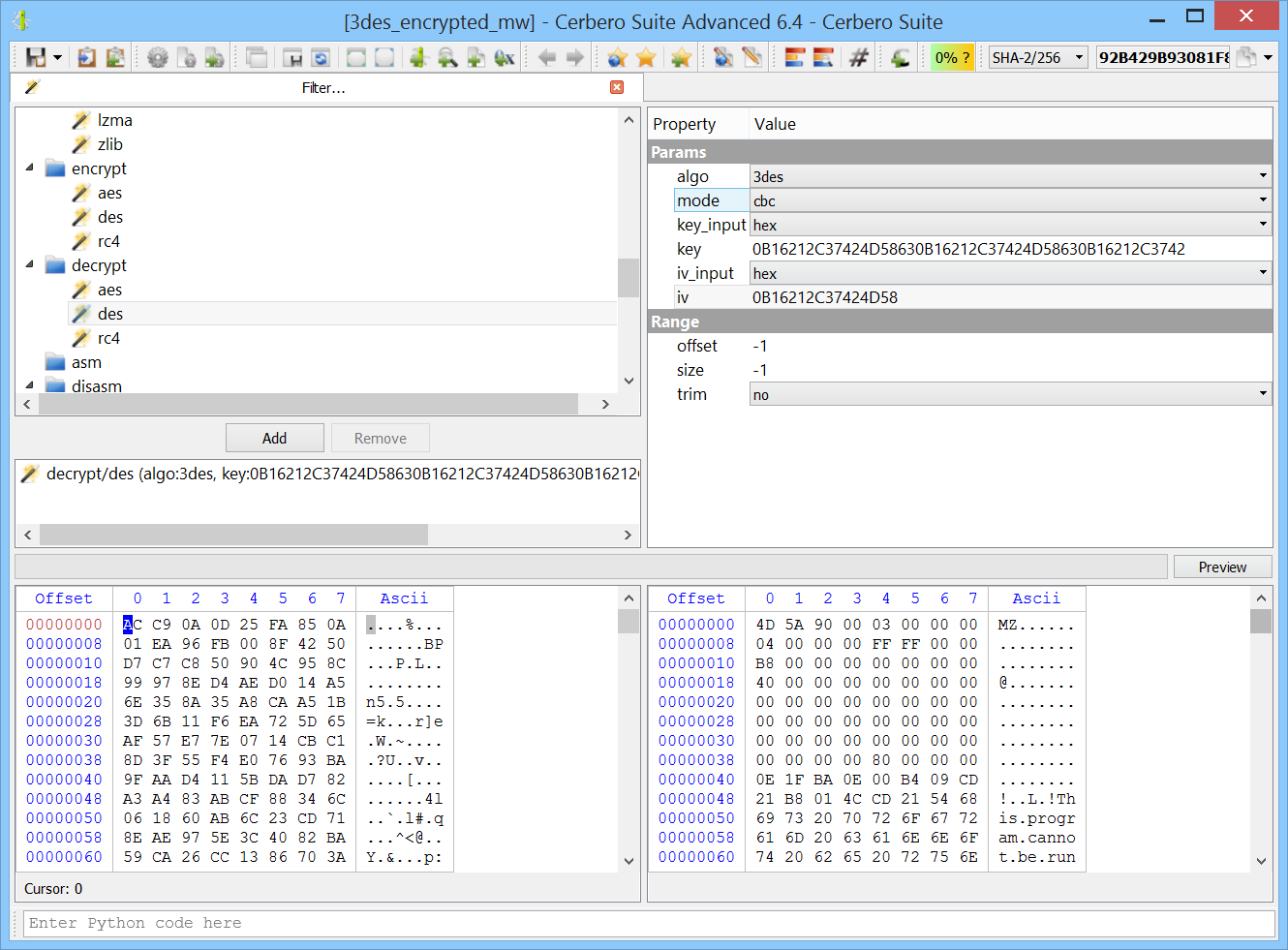
DES Filter
We’ve added the DES crypto filter which supports DES, DEX and 3DES. While the DES algorithm family is no longer recommended for encryption, it can still be found in malware.
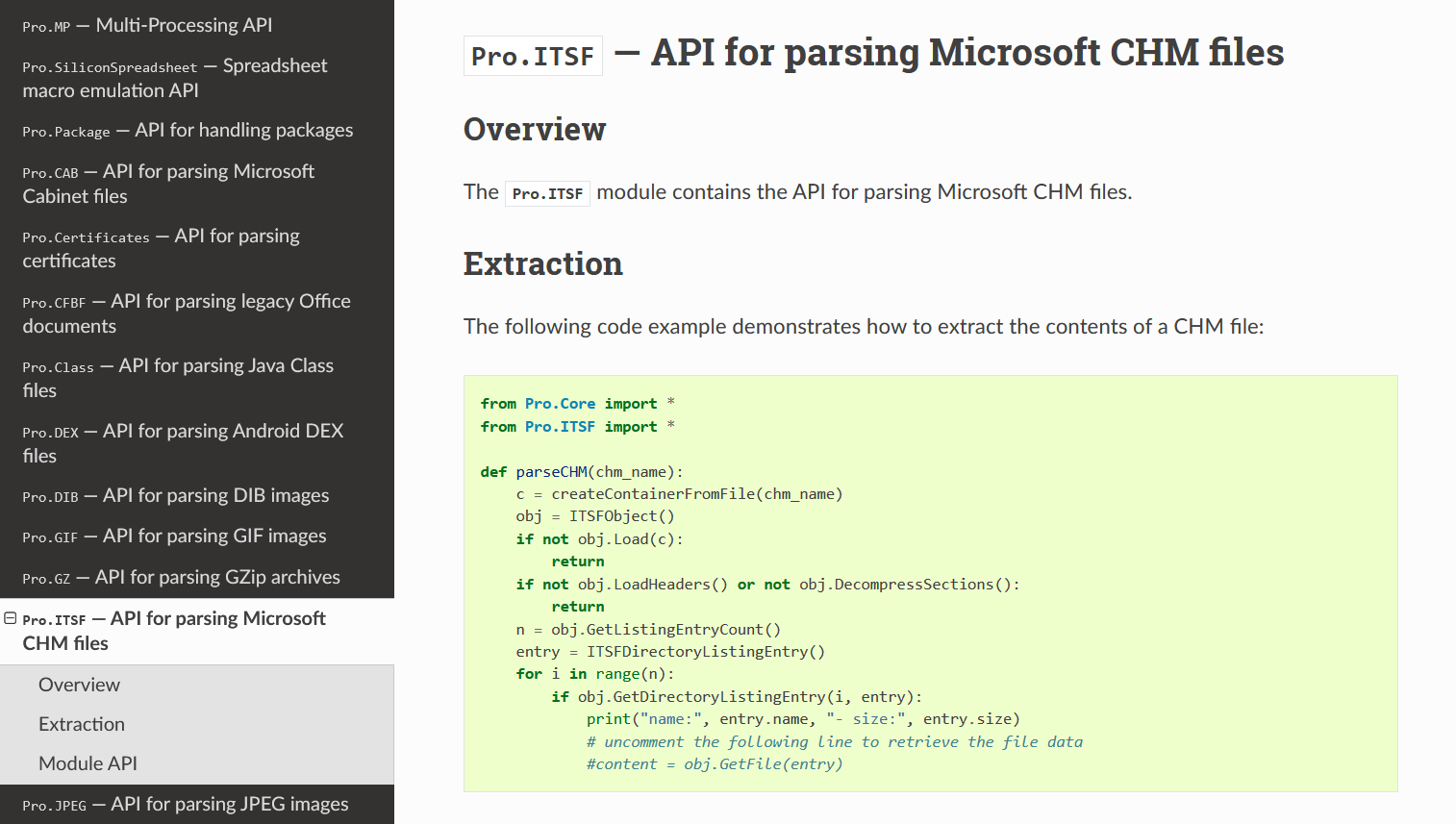
ITSF & JPEG module documentation
We have documented the ITSF module which provides the API for parsing Microsoft CHM files and the JPEG module.
Improved command line interpreter
We’ve improved the command line interpreter control and workspaces can now add their own interpreters.