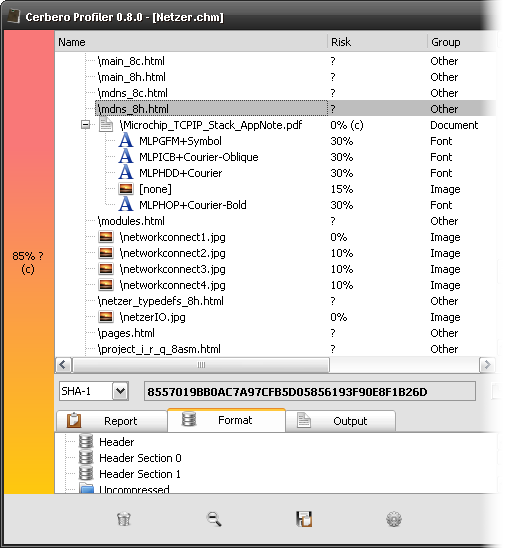
We recently stumbled upon this tweet by @Cryptolaemus1 about a malicious OneNote document with an embedded ISO file. Because of our recently released ISO Format package, we thought it would be interesting to analyze this malware sample with Cerbero Suite.
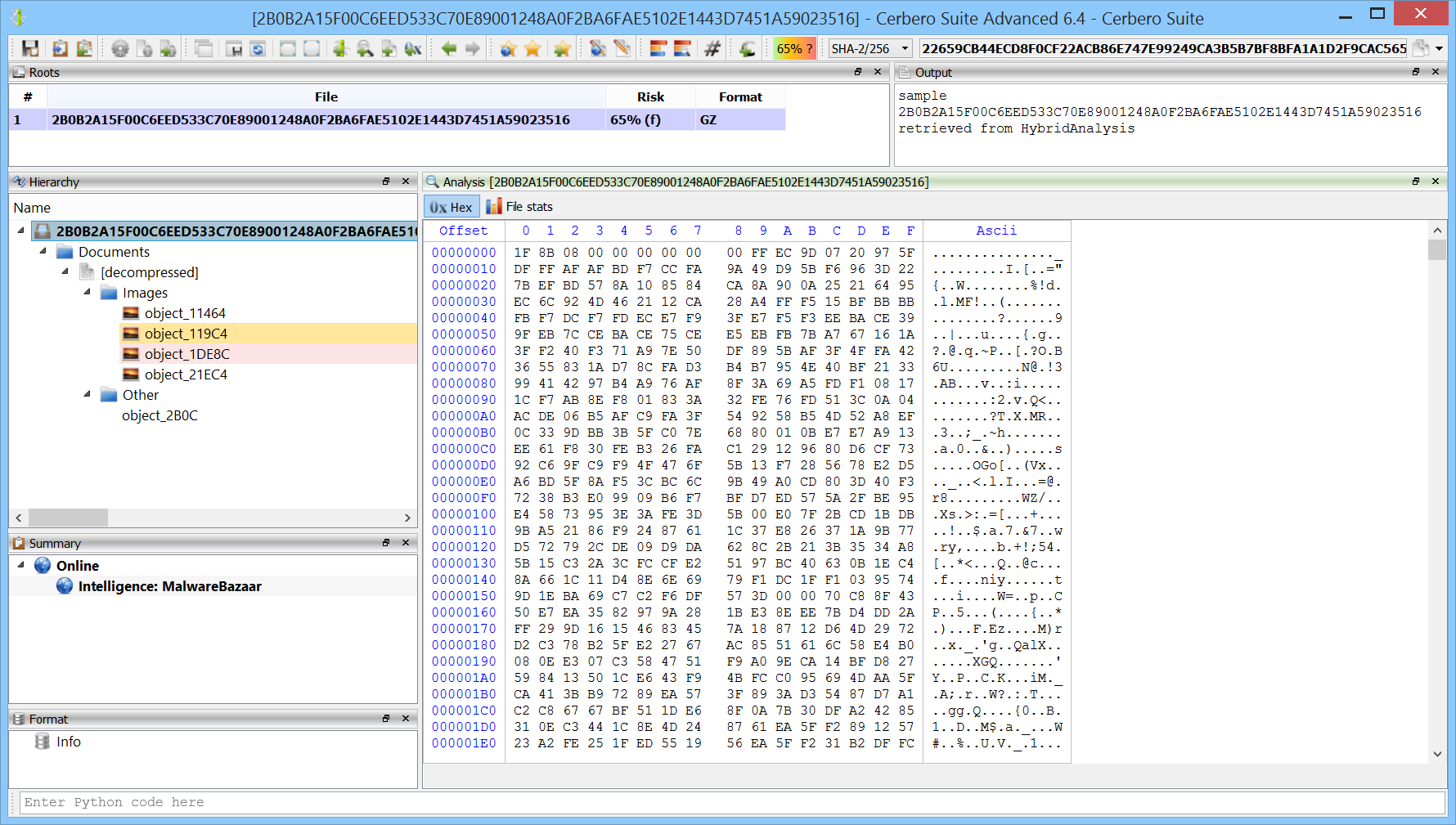
SHA256: 2B0B2A15F00C6EED533C70E89001248A0F2BA6FAE5102E1443D7451A59023516
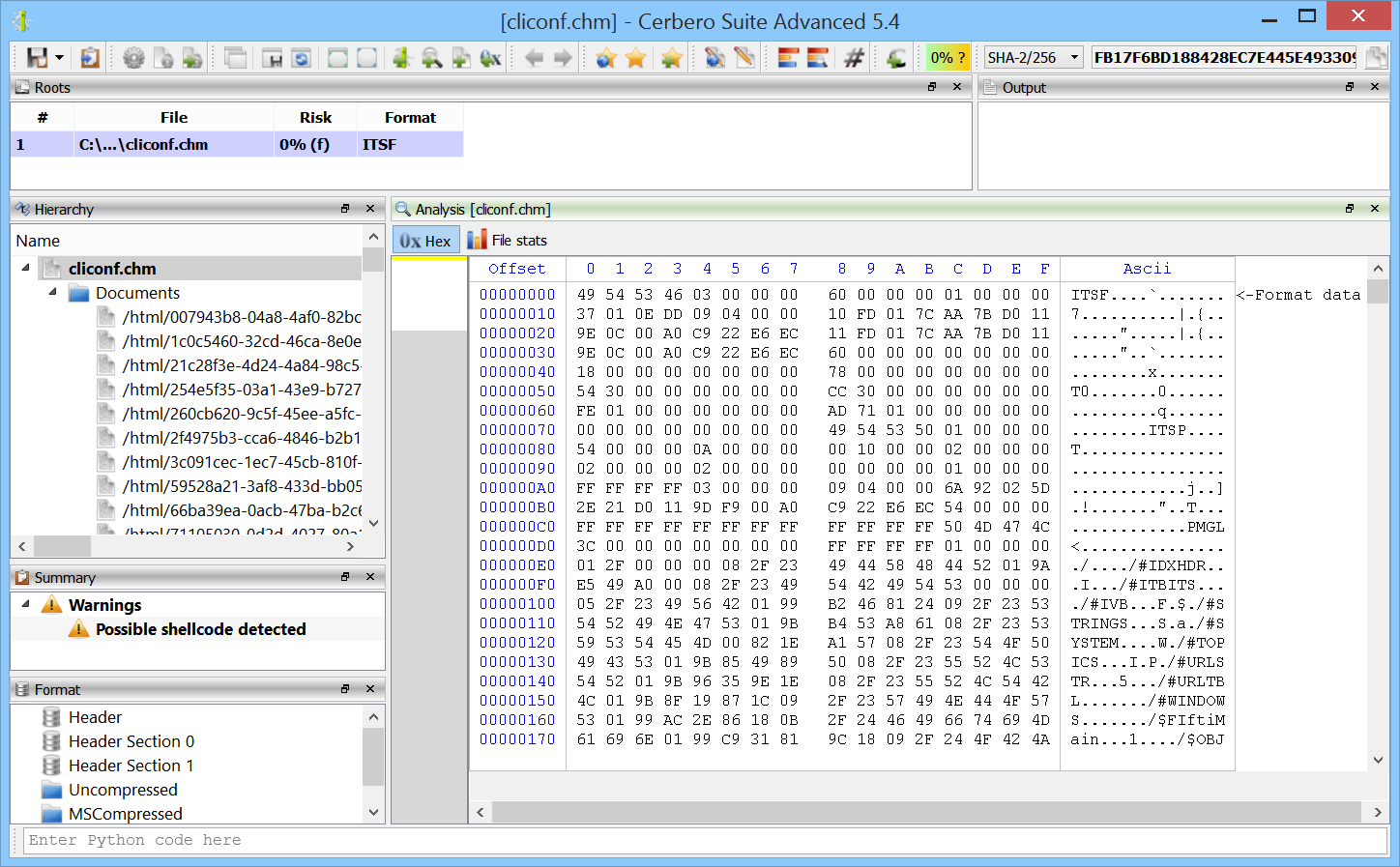
The unidentified embedded object in the OneNote document is an ISO file.