We’re happy to announce the release of Cerbero Suite 8.4 and Cerbero Engine 5.4. This might be a minor version, but we’ve added some important features that have been on our list for a while.
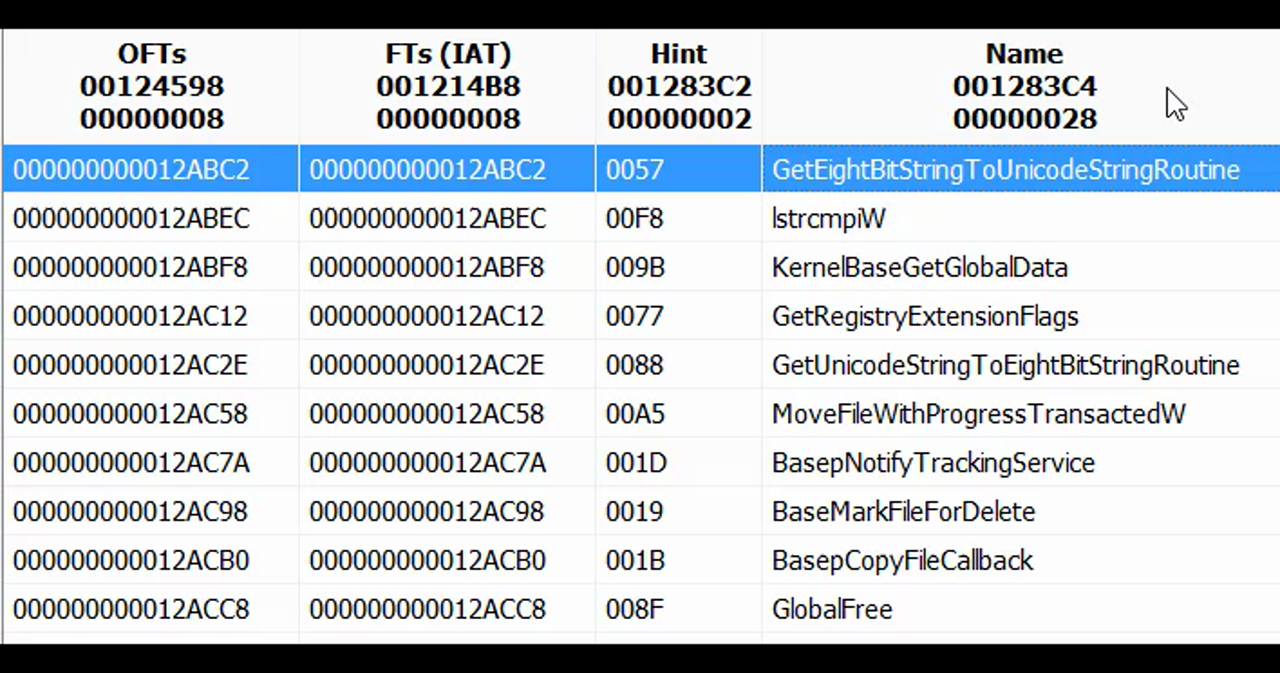
Table Sorting
This has been a long time coming—most tables in Cerbero Suite can now be sorted. If a plugin uses the default table control, sorting works automatically without any extra effort.