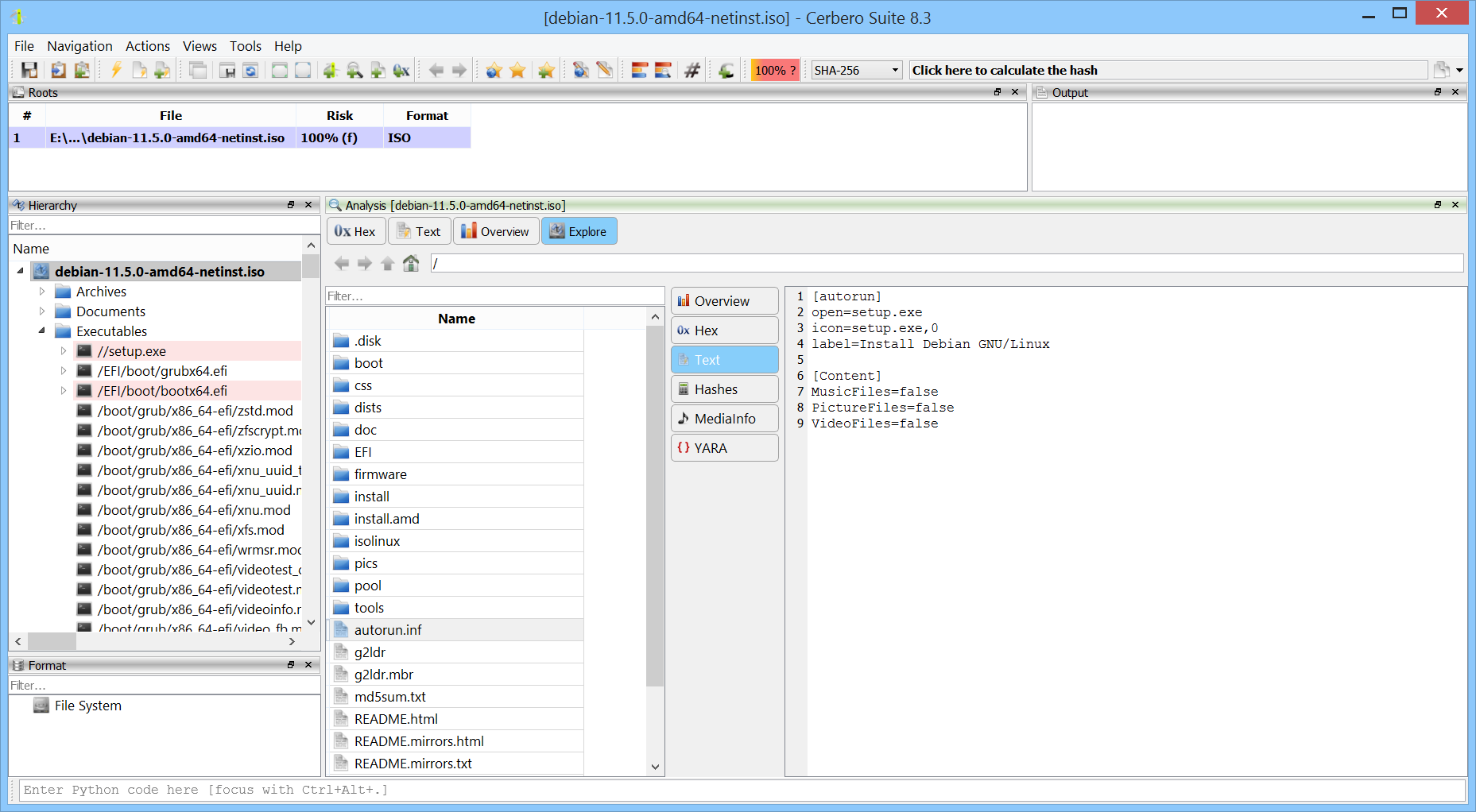
Our ISO Format package, which supports the ISO9660 and UDF file systems, used to be slow when handling larger file systems. We’ve completely rewritten it, and now it performs effortlessly.
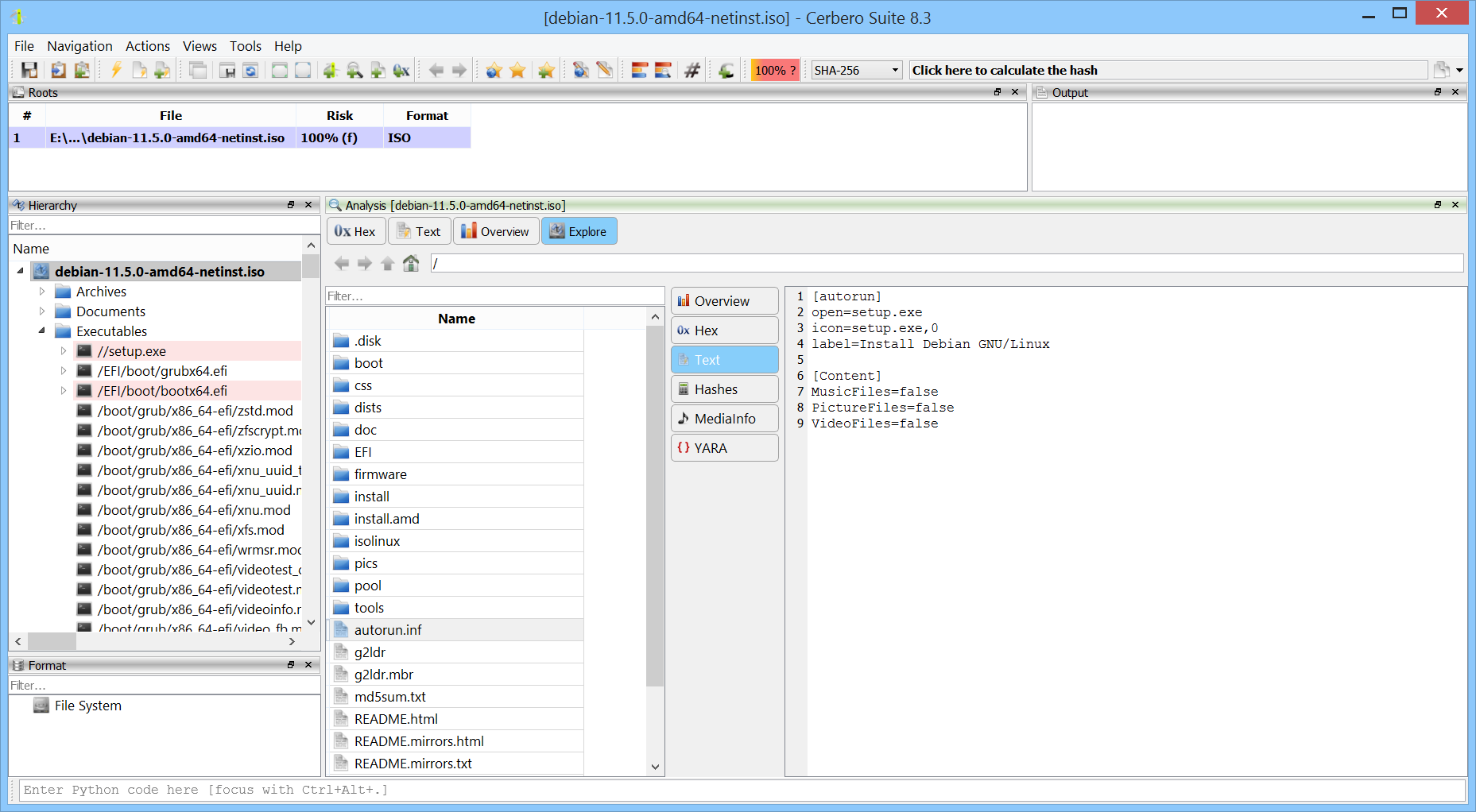
Our ISO Format package, which supports the ISO9660 and UDF file systems, used to be slow when handling larger file systems. We’ve completely rewritten it, and now it performs effortlessly.
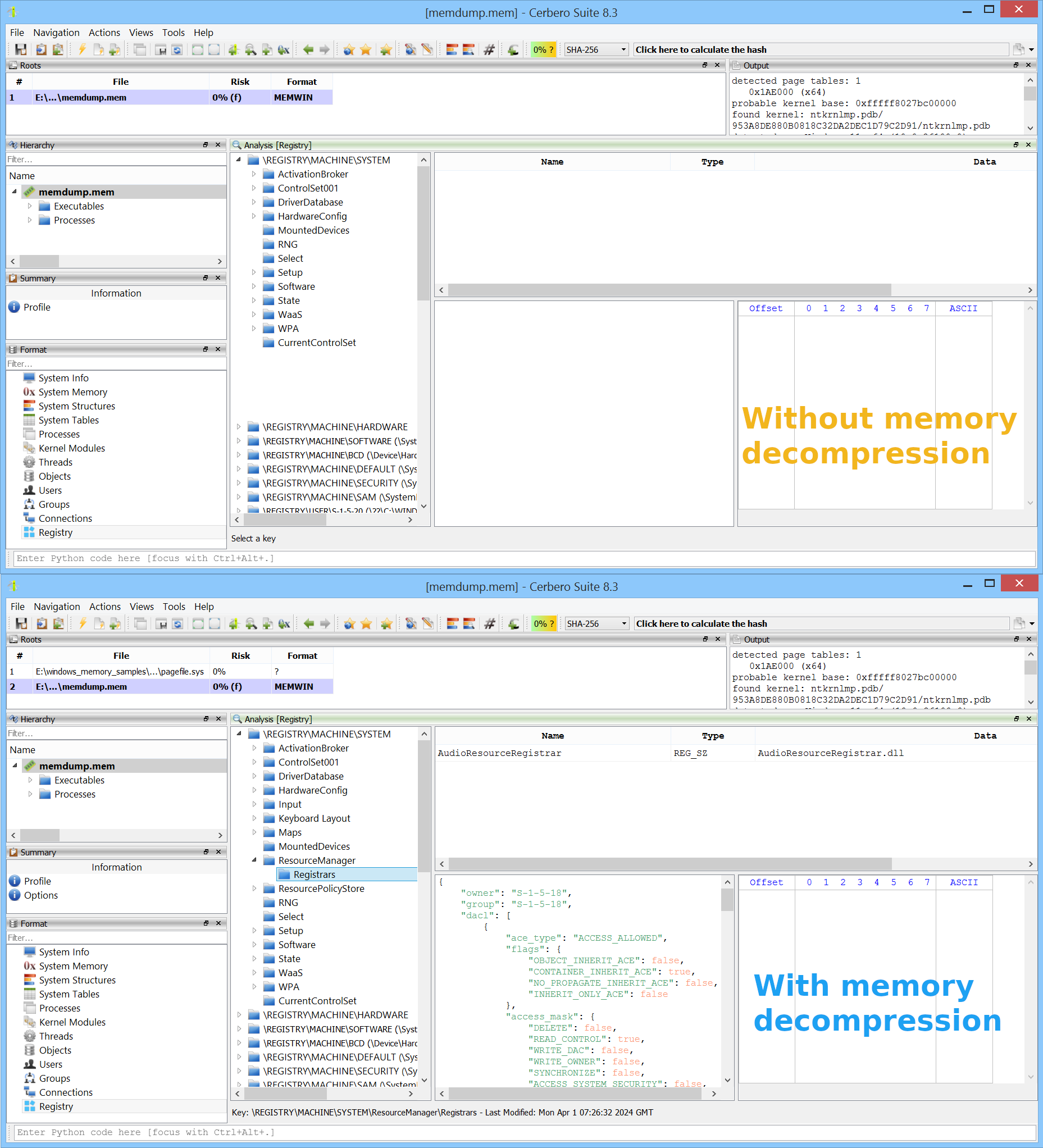
Windows 10 (version 1507) introduced memory compression, a feature that allows certain memory pages to be compressed and managed by the “MemCompression” process. As a result, in a memory snapshot, some pages may be unavailable because they reside in compressed memory. Memory compression in Windows is optional and can be disabled if desired, but it is enabled by default.
We are excited to announce the release of version 0.2 of our Memory Analysis package, currently in beta, which adds support for memory decompression and reading paged-out memory from pagefiles.
In the example image below, we can see a case where certain registry keys are missing when examining a memory snapshot—these keys are located in memory pages that have been compressed. In the lower part of the image, after enabling memory decompression, the previously missing keys become visible.
We released Cerbero Suite 8.3 and Cerbero Engine 5.3! While we have introduced many small improvements and expanded our SDK, most of the work for this release is “under the hood.” Shortly, we will release many new packages that benefit from the improvements we have added.
We’ve updated the Windows Crash Dump Format package to support inspecting kernel memory dumps through the Memory Analysis package.
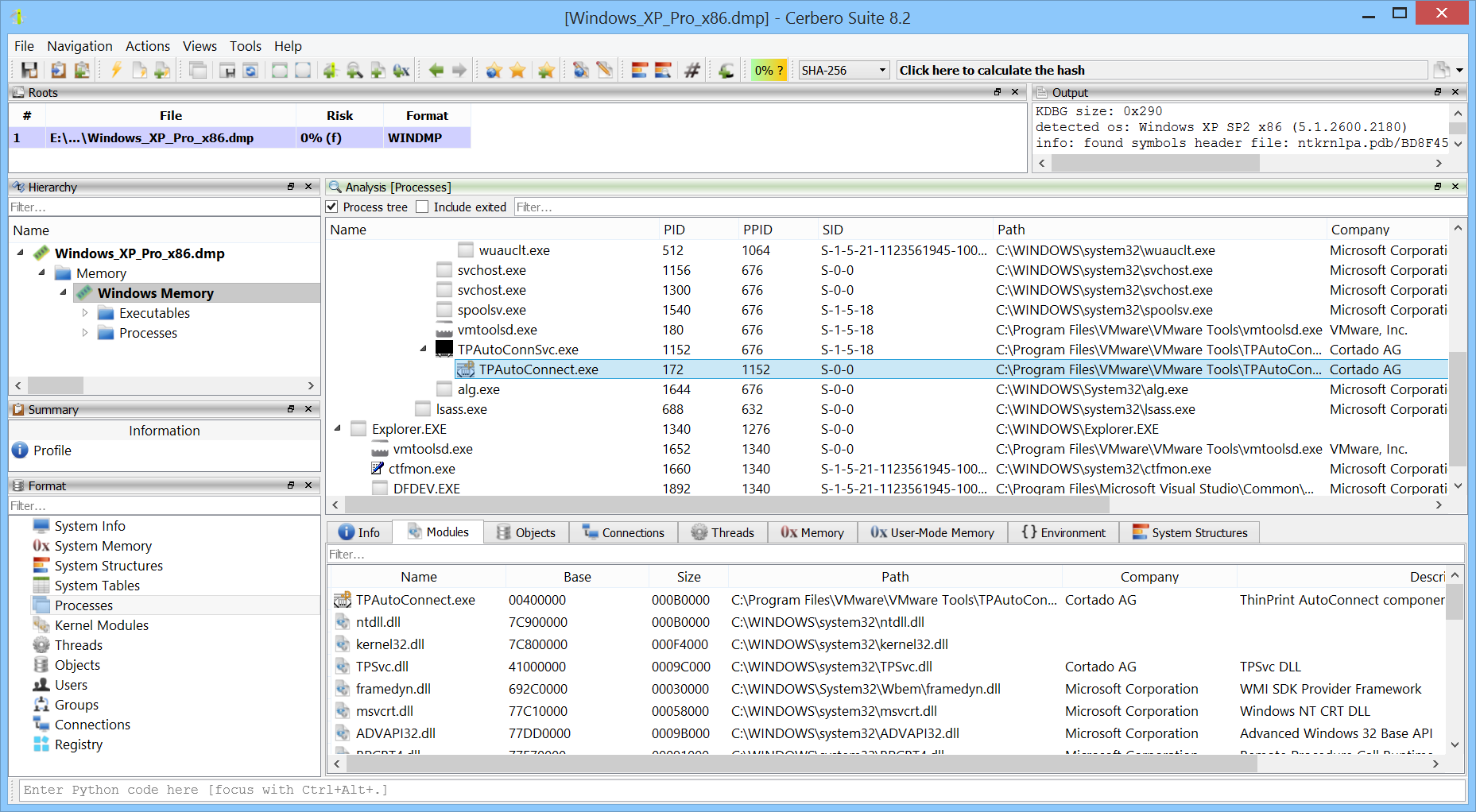
We’re excited to announce the release of the new Memory Analysis package, capable of analyzing memory dumps from all Windows versions, from XP to 11, both x86 and x64.
The package will be available to all licenses of Cerbero Suite. Today we’re rolling out the beta for all commercial licenses, and it will be accessible to all licenses once the beta period ends. This new package replaces the previous Windows Memory Analysis package.
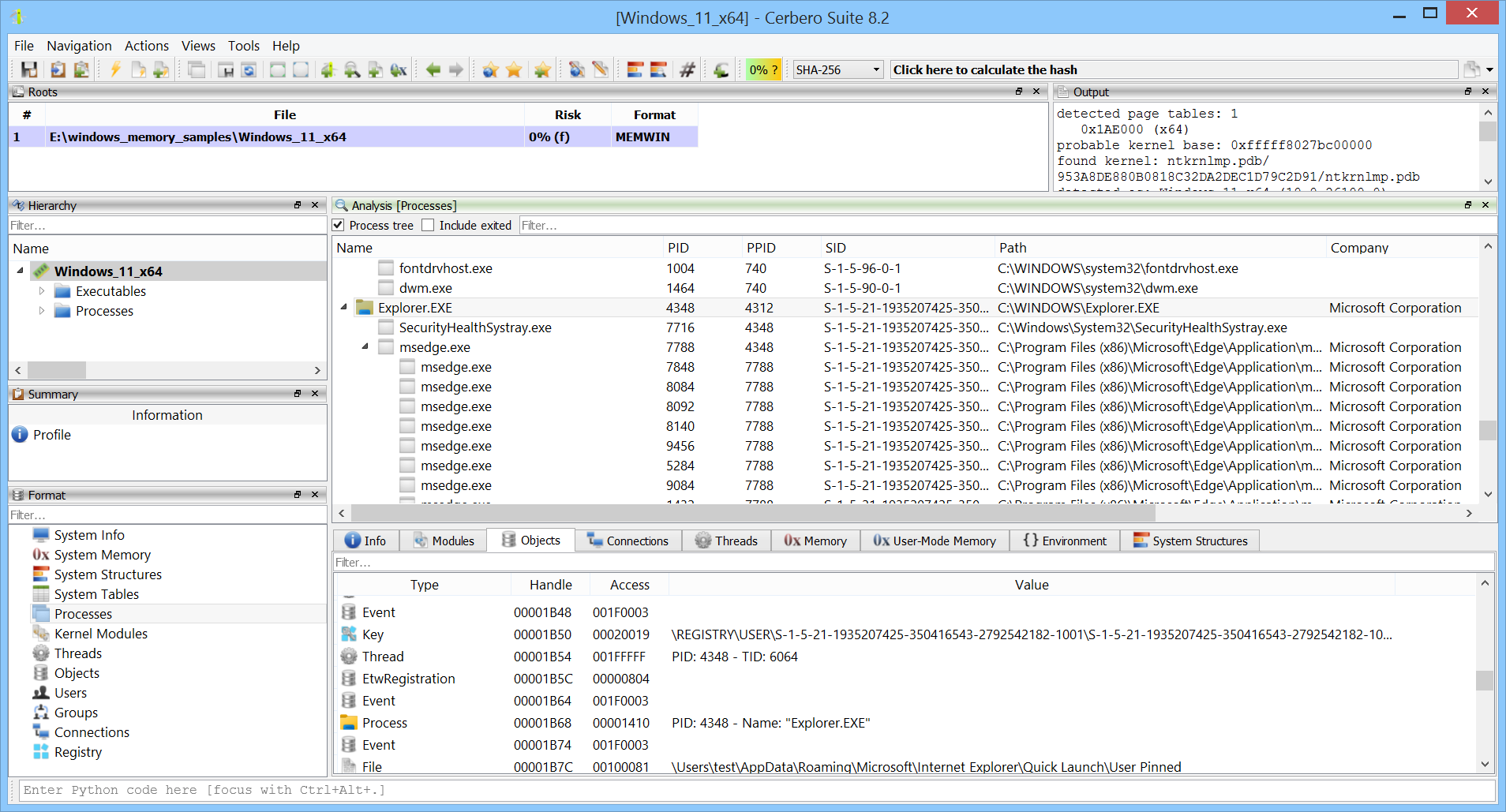
We’re excited to release Cerbero Suite 8.2 and Cerbero Engine 5.2!
This release includes many improvements, with the most significant being the introduction of the Memory Analysis package. We encourage you to read the blog post about it for more details. Additionally, it’s worth mentioning that the Windows crash dump format has been moved to an optional package and is no longer included with the main binary.
We’re excited to release Cerbero Suite 8.1 and Cerbero Engine 5.1!
The main highlight of this release is that we have finally completed the documentation of the SDK. However, there are also some other news which we’ll be discussing in this post.
We have completed the documentation of the SDK, including built-in file formats, installable packages, and external modules.
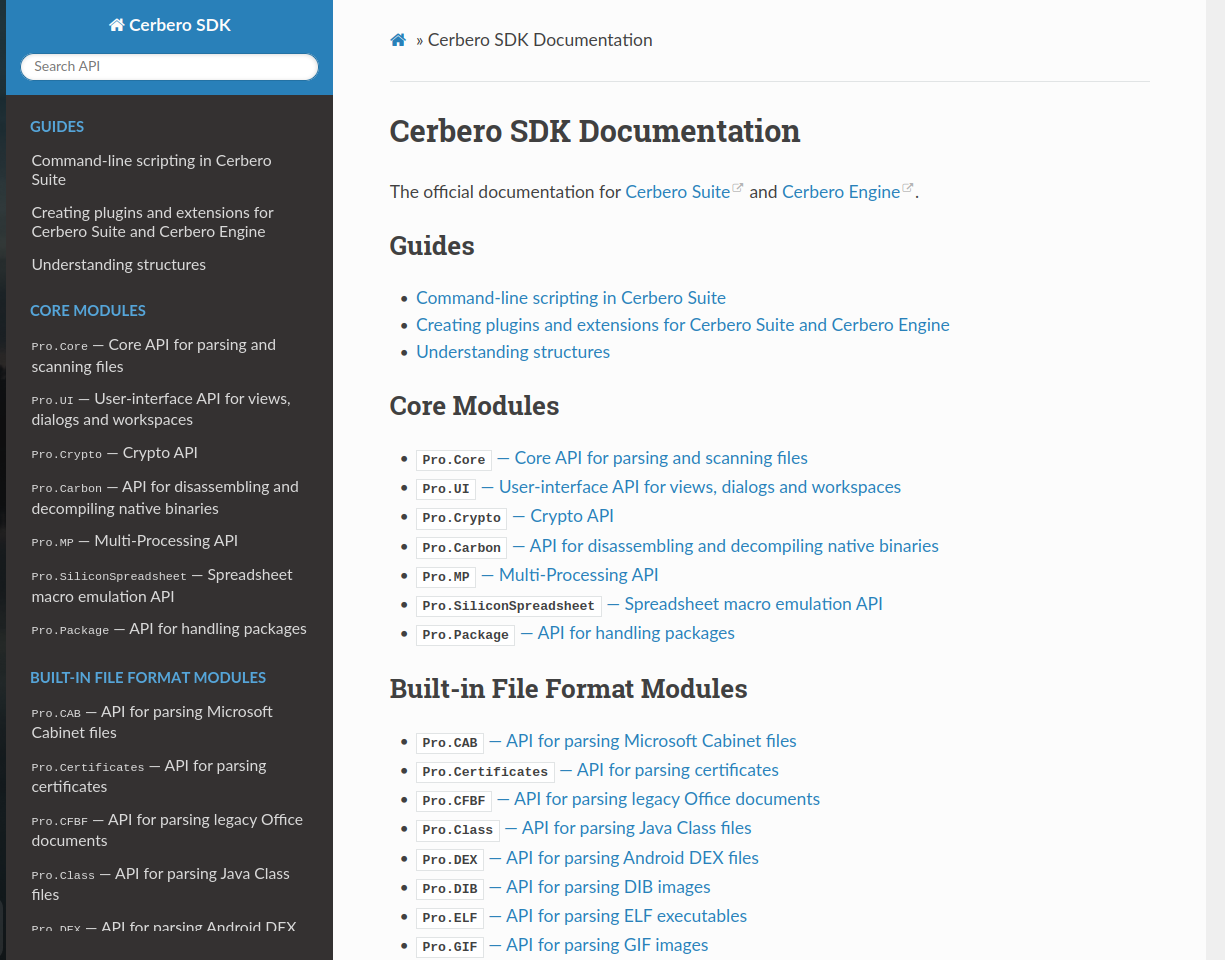
This means that the entire SDK is now available for auto-completion in the Python editor. Every time you install a package that is exposed to the SDK, auto-completion becomes available for that package as well.
The SDK of Cerbero Suite and Cerbero Engine is unparalleled in scope and depth, offering a vast array of functionalities for developers. With the documentation, you can easily explore all the capabilities the SDK has to offer. Whether you’re writing plugins to automate tasks, analyzing complex file formats, or creating new tools, the SDK provides the necessary tools and resources.
The integrated Python editor in Cerbero Suite further enhances your development experience by providing features like syntax highlighting, hints and code completion. To get started, simply navigate to the SDK documentation website, where you’ll find extensive guides, API references, and examples. The documentation is organized to help both beginners and advanced users quickly find the information they need.
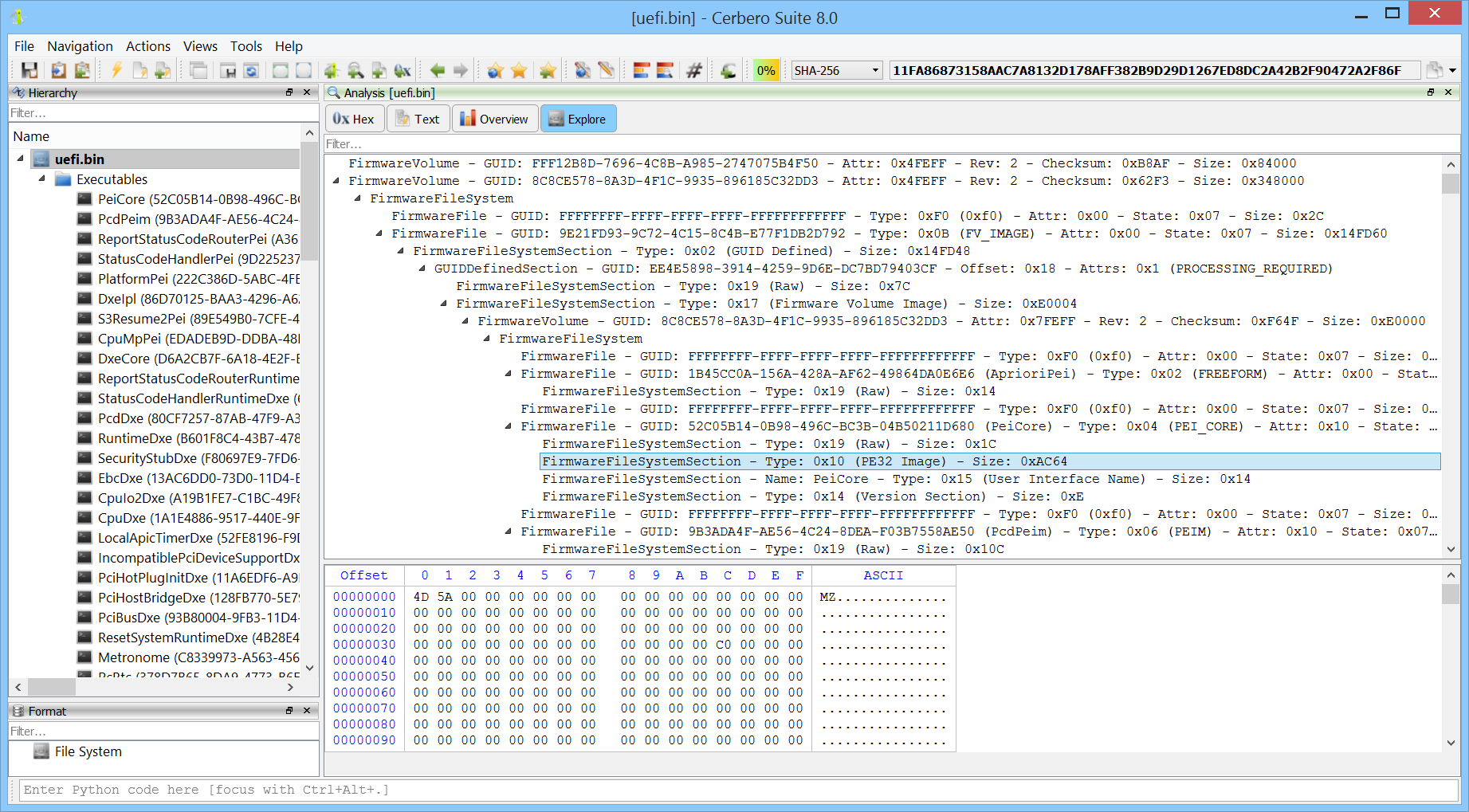
We have released the UEFI Firmware Image Format package for all licenses of Cerbero Suite!
The package supports a variety of UEFI firmware image formats and, in addition to allowing you to inspect their structure, it automatically extracts embedded files.
The AbuseCH Intelligence package to access intelligence from MalwareBazaar is now available to personal licenses of Cerbero Suite!
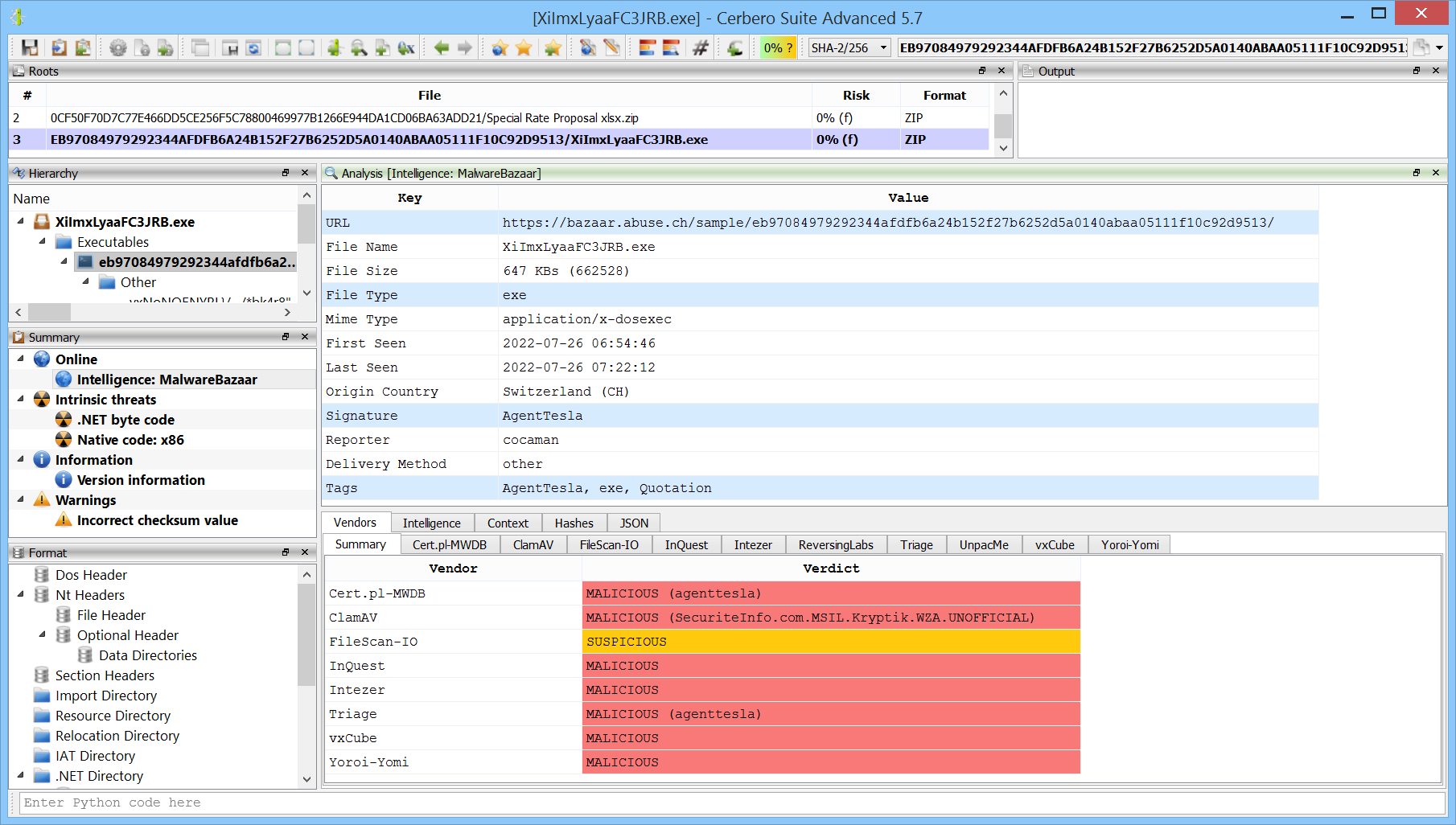
If you’re not yet familiar with the AbuseCH Intelligence package, you can check out the video presentation to quickly learn about its features.
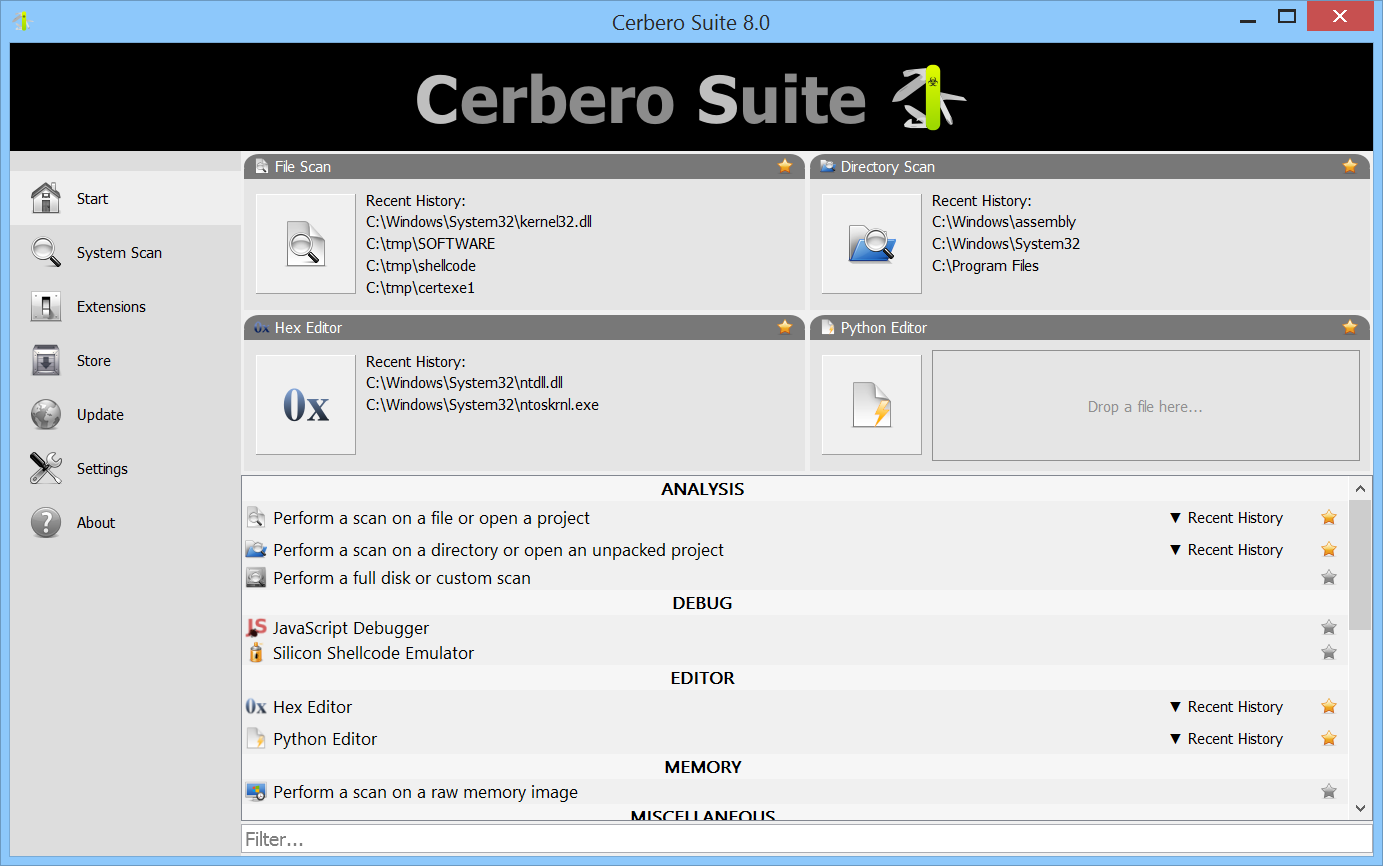
We are excited to announce the release of Cerbero Suite 8 and Cerbero Engine 5! All our customers with a valid license can now upgrade directly within the application.
In this major release, we’ve revamped the start page to enhance accessibility to the various logic providers and introduced customizable panels. Now, you can select your preferred tools and position them prominently for quick access upon launching Cerbero Suite.