We are happy to announce support for the Windows Event Log (EVTX) format. The new EVTX Format package lets you inspect EVTX files directly within the application, with a familiar table-based event viewer and full XML detail pane.
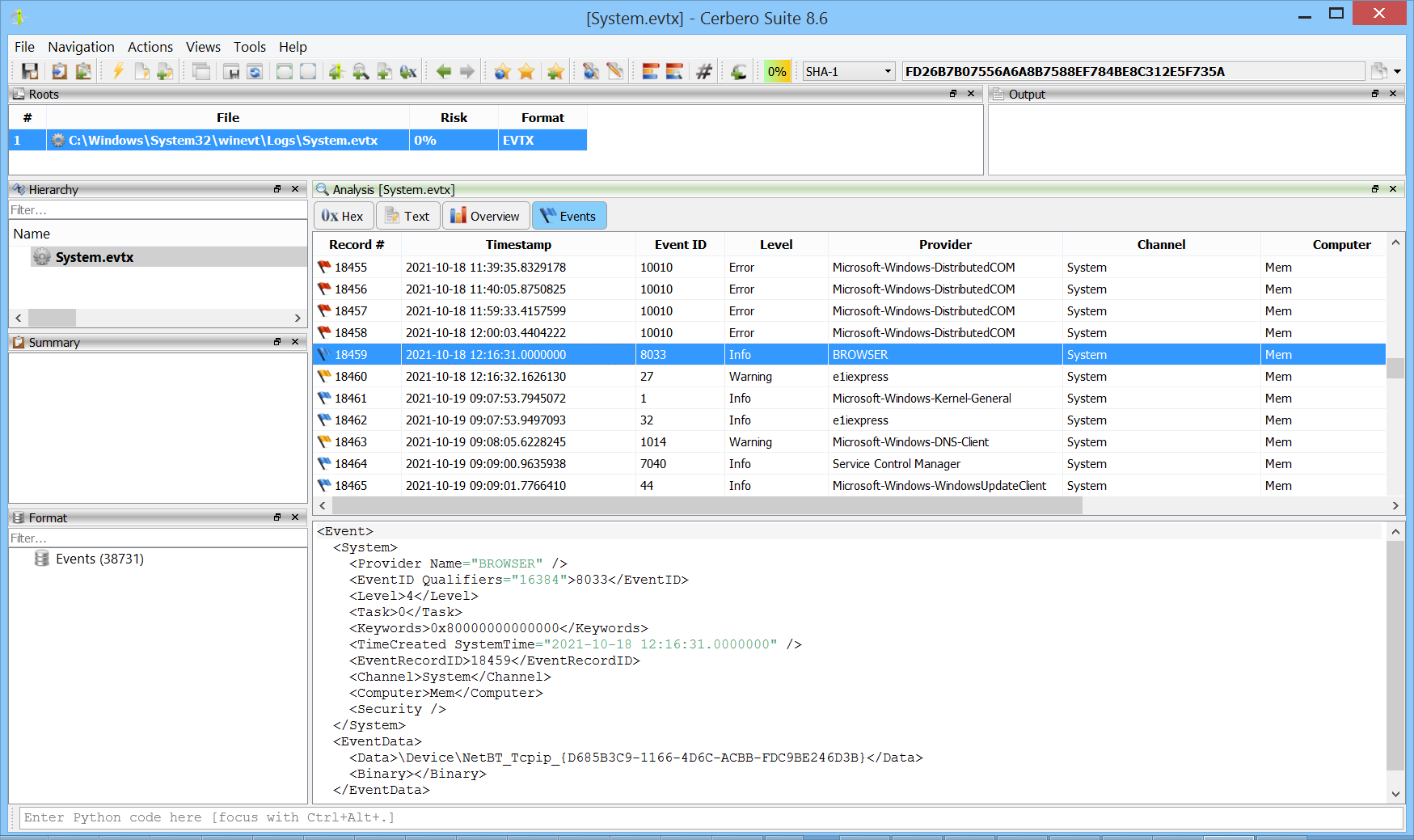
EVTX is the binary log format used by modern versions of Windows (Vista and later) to store system, security, and application events. It is a key artifact in digital forensics and incident response, as it records user logons, process creation, service changes, and many other system activities. Having native support in Cerbero Suite means analysts can open and triage event logs without leaving their primary analysis environment.