We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on Hack The Box, so credit goes to them for creating it.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on Hack The Box, so credit goes to them for creating it.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on the Memory Forensic site, so credit goes to them for highlighting it and to Hack The Box for creating it in the first place.
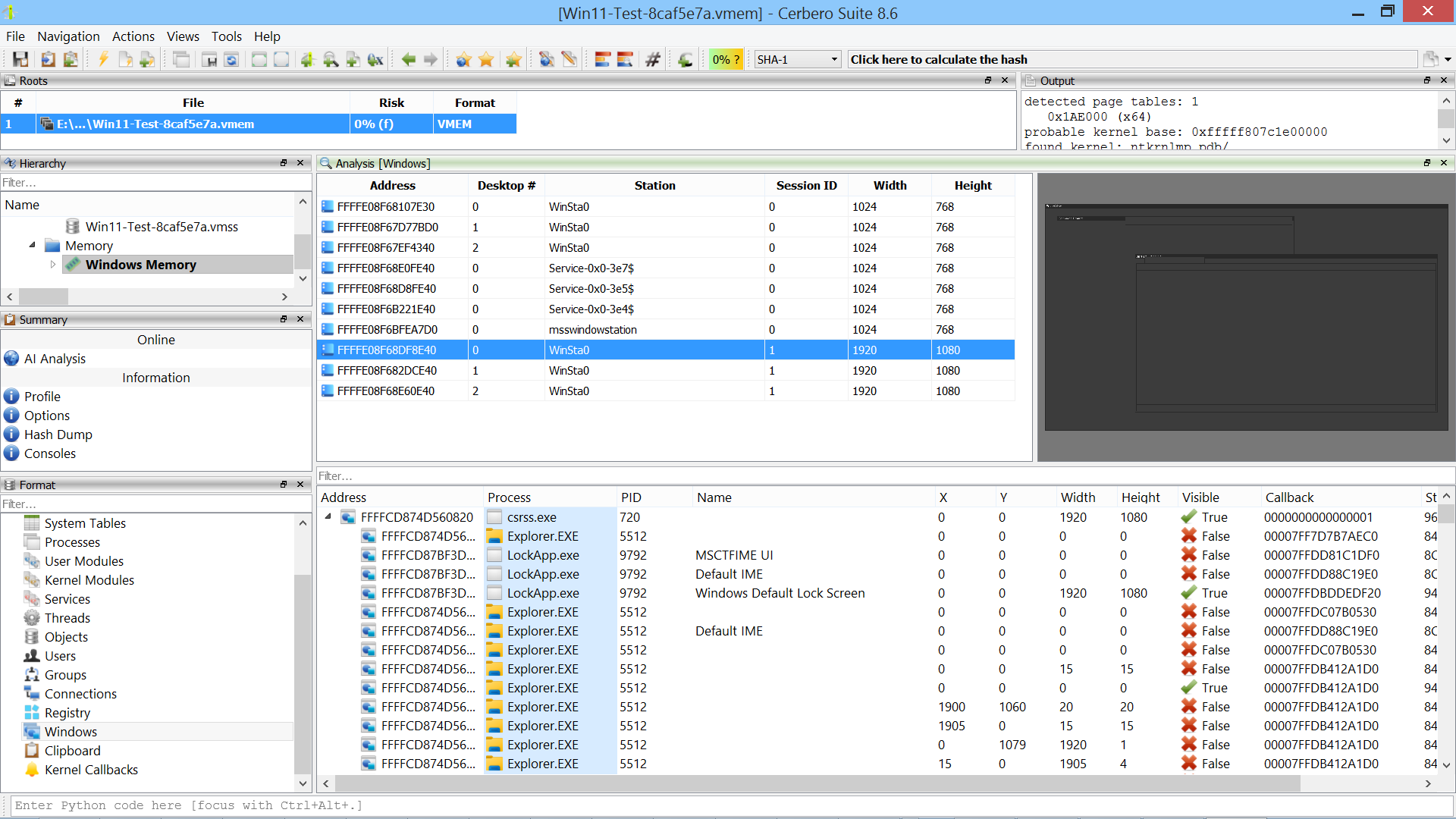
We are excited to announce the release of Memory Analysis 0.9 package, a significant milestone that introduces support for extracting GUI artifacts.
All features have been thoroughly tested across Windows versions from XP through Windows 11, on both x86 and x64 architectures. This, for instance, is the latest version of Windows 11.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on the Memory Forensic site, so credit goes to them for highlighting it and to MemLabs for creating it in the first place.
Continue reading “Memory Challenge 16: MemLabs Lab 1 – Beginner’s Luck”
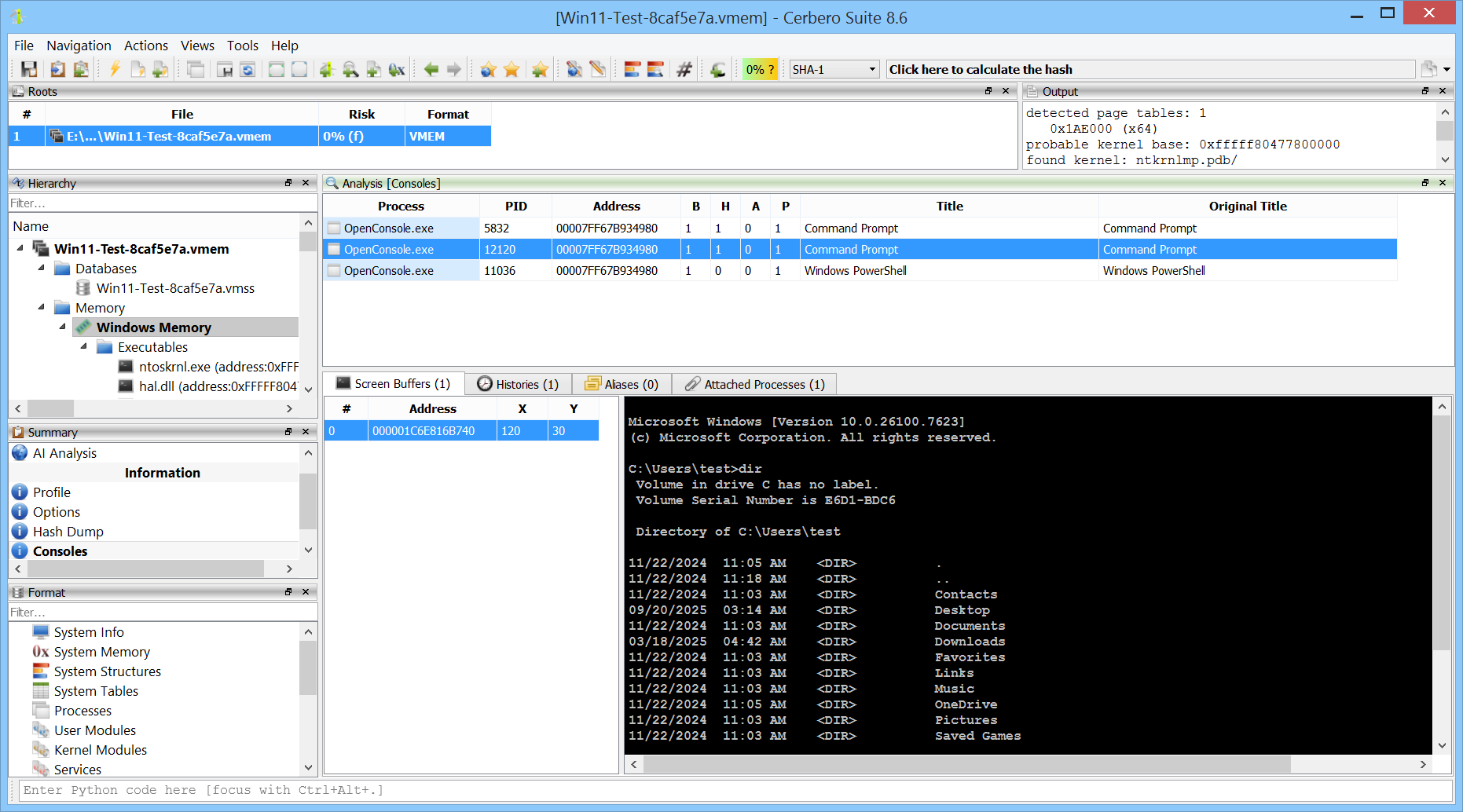
We are excited to announce the release of the Memory Analysis 0.8 package. The main feature of this version is the introduction of console information extraction.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on Hack The Box, so credit goes to them for creating it.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on the Memory Forensic site, so credit goes to them for highlighting it and to Hack The Box for creating it in the first place.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on the Memory Forensic site, so credit goes to them for highlighting it and to CyberDefenders for creating it in the first place.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on the Memory Forensic site, so credit goes to them for highlighting it and to CyberDefenders for creating it in the first place.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online.
We found this challenge on Hack The Box, so credit goes to them for creating it.