We are happy to announce support for the SquashFS file system format. The new SquashFS Format package lets you browse and extract files from SquashFS images directly within the application.
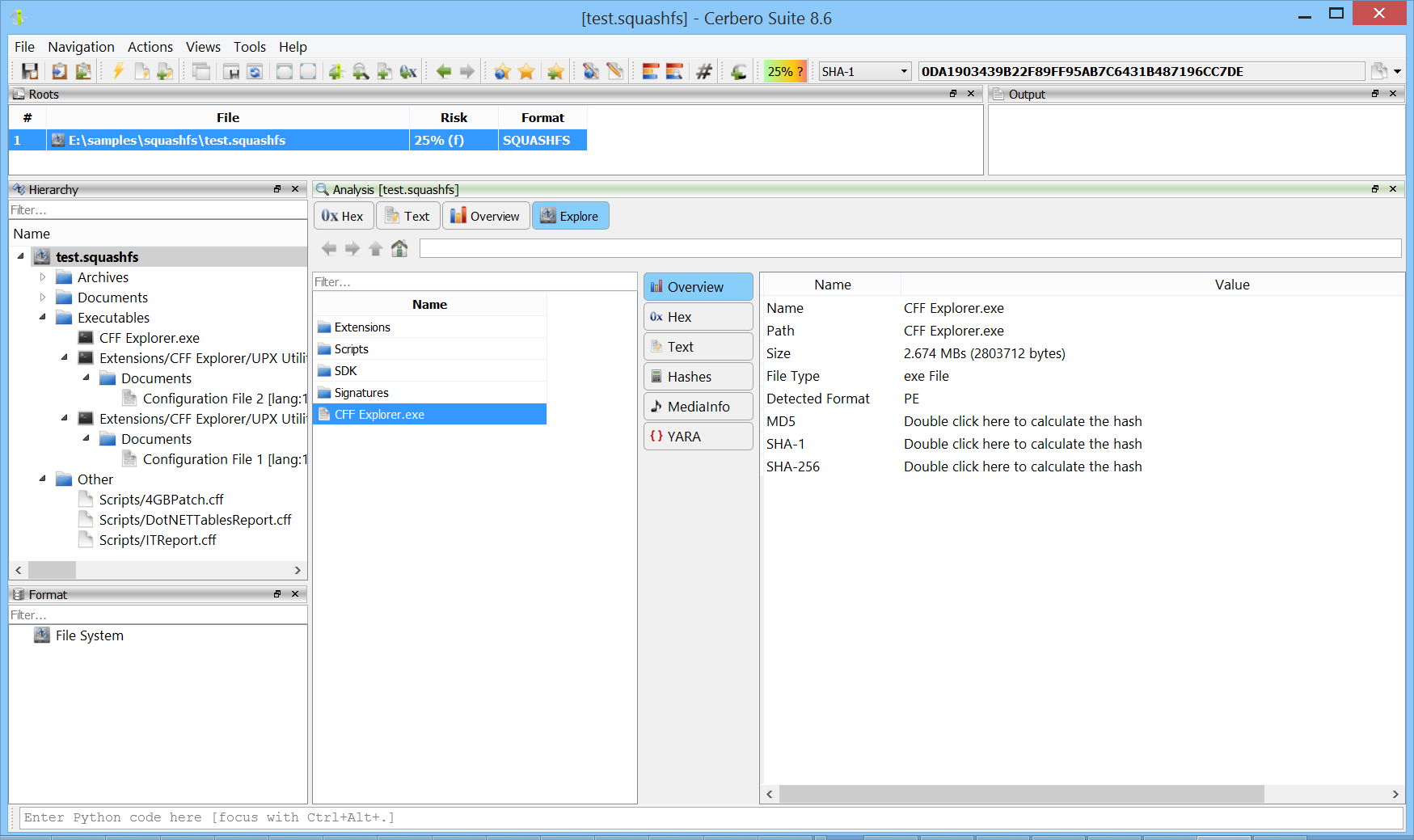
SquashFS is a compressed, read-only file system widely used in Linux distributions, embedded devices, firmware images, container technologies, and snap/AppImage application packages. It supports multiple compression algorithms and is designed for high compression ratios with fast random access. Having native support in Cerbero Suite means analysts can inspect SquashFS images encountered during firmware analysis, malware triage, or forensic investigations without needing external tools.