We’ve released version 0.6 of the Memory Analysis package, currently in beta.
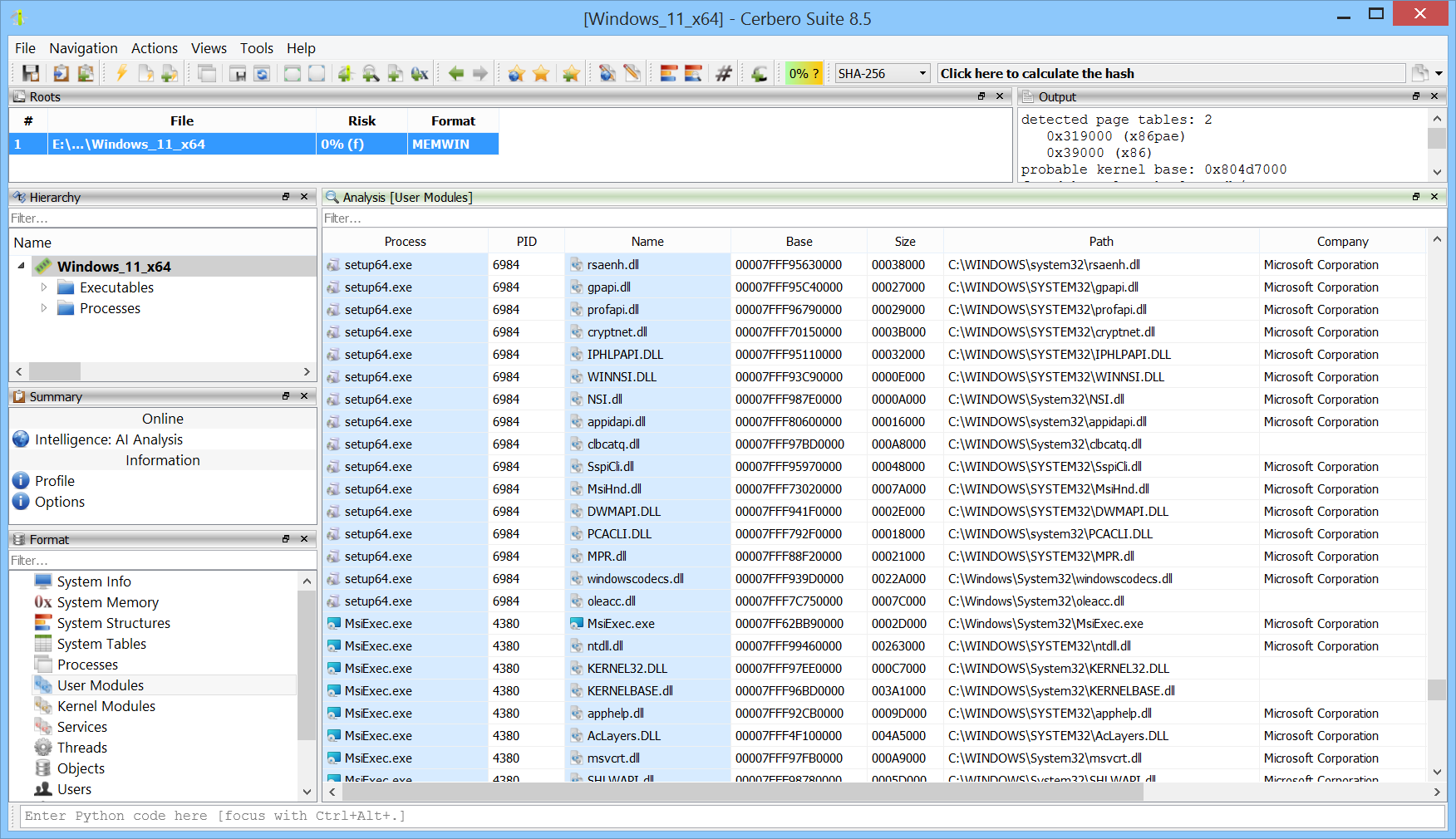
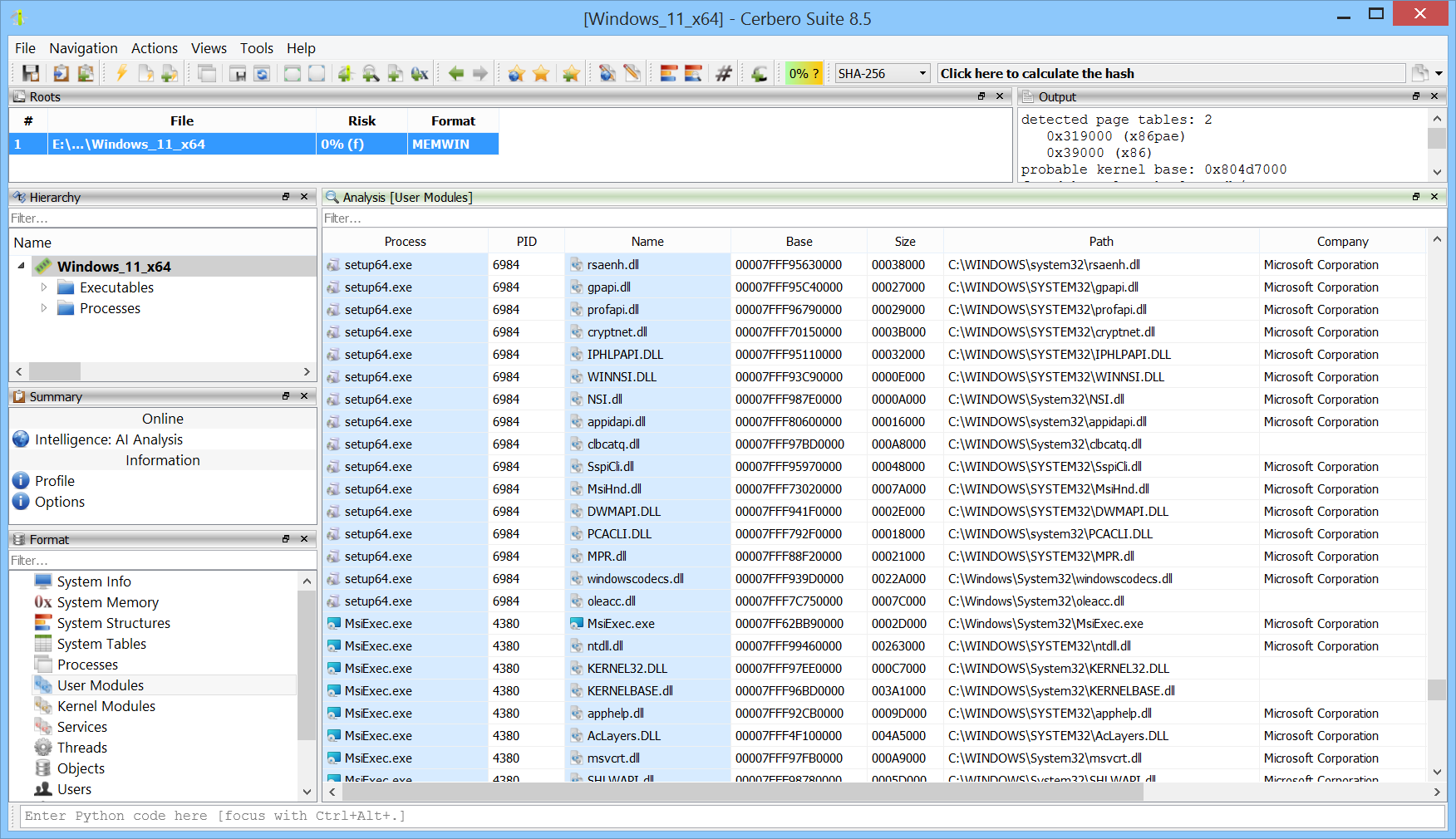
All user modules from all processes can now be inspected at once. This makes it easy to discover which processes load a particular module.
We’ve released version 0.6 of the Memory Analysis package, currently in beta.
All user modules from all processes can now be inspected at once. This makes it easy to discover which processes load a particular module.
We’re testing our Memory Analysis package (currently in beta) against various challenges available online. In this case, we combined the memory analysis with our soon-to-be-released AI Assistant package to solve the challenge in an automated way.
The challenge was created by the CyberDefenders team and can be downloaded from their website.
We’ve released the NSIS Format package, which adds support for the Nullsoft Scriptable Install System format.
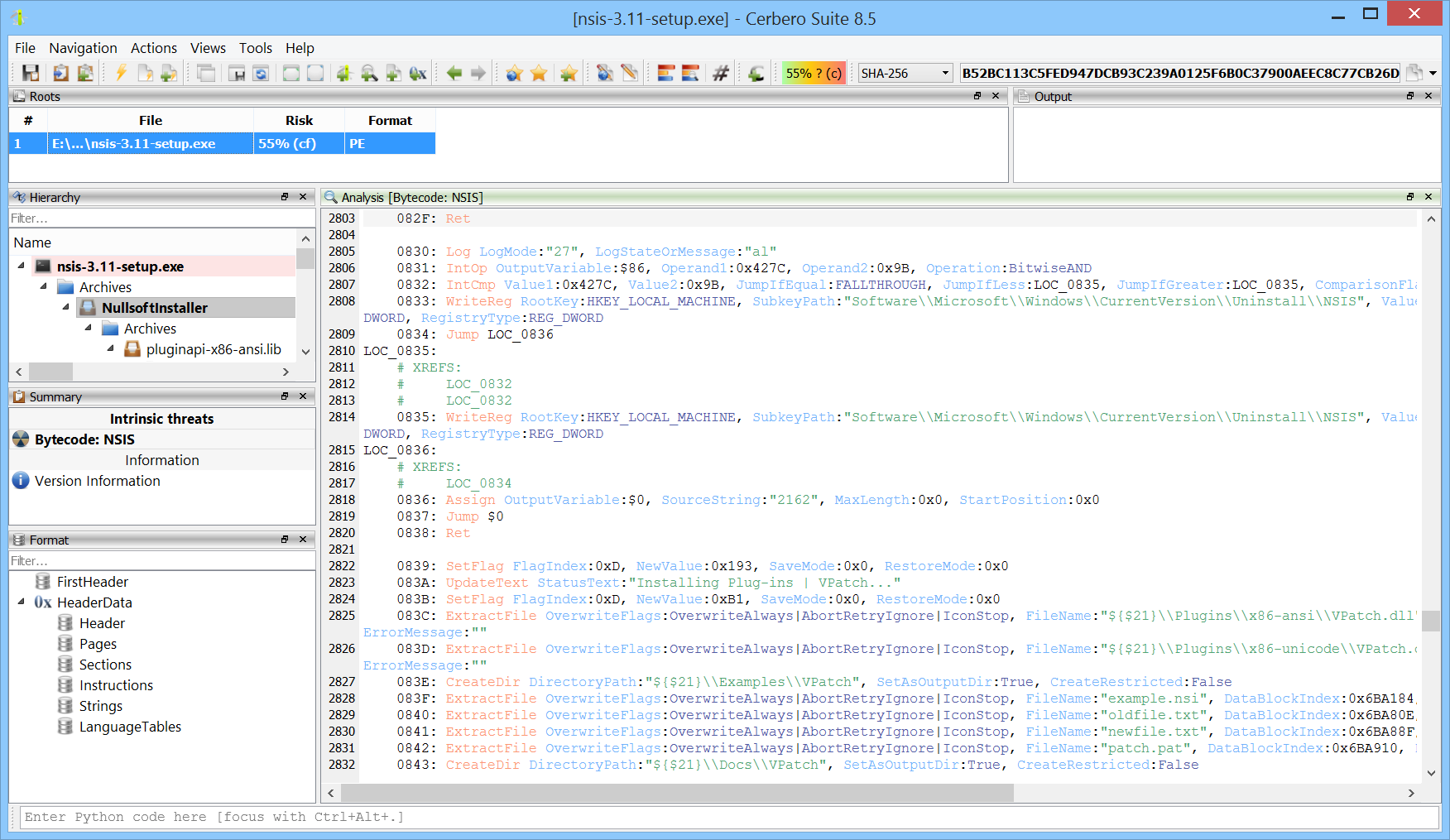
NSIS (Nullsoft Scriptable Install System) is an open-source tool used to create Windows installers. It allows developers to build lightweight, fast, and customizable installation packages through a scripting language that provides fine-grained control over the installation process.
The NSIS Format package provides state-of-the-art support for all versions of NSIS 2 and 3. It allows both the inspection of the format and complete disassembly of the bytecode.
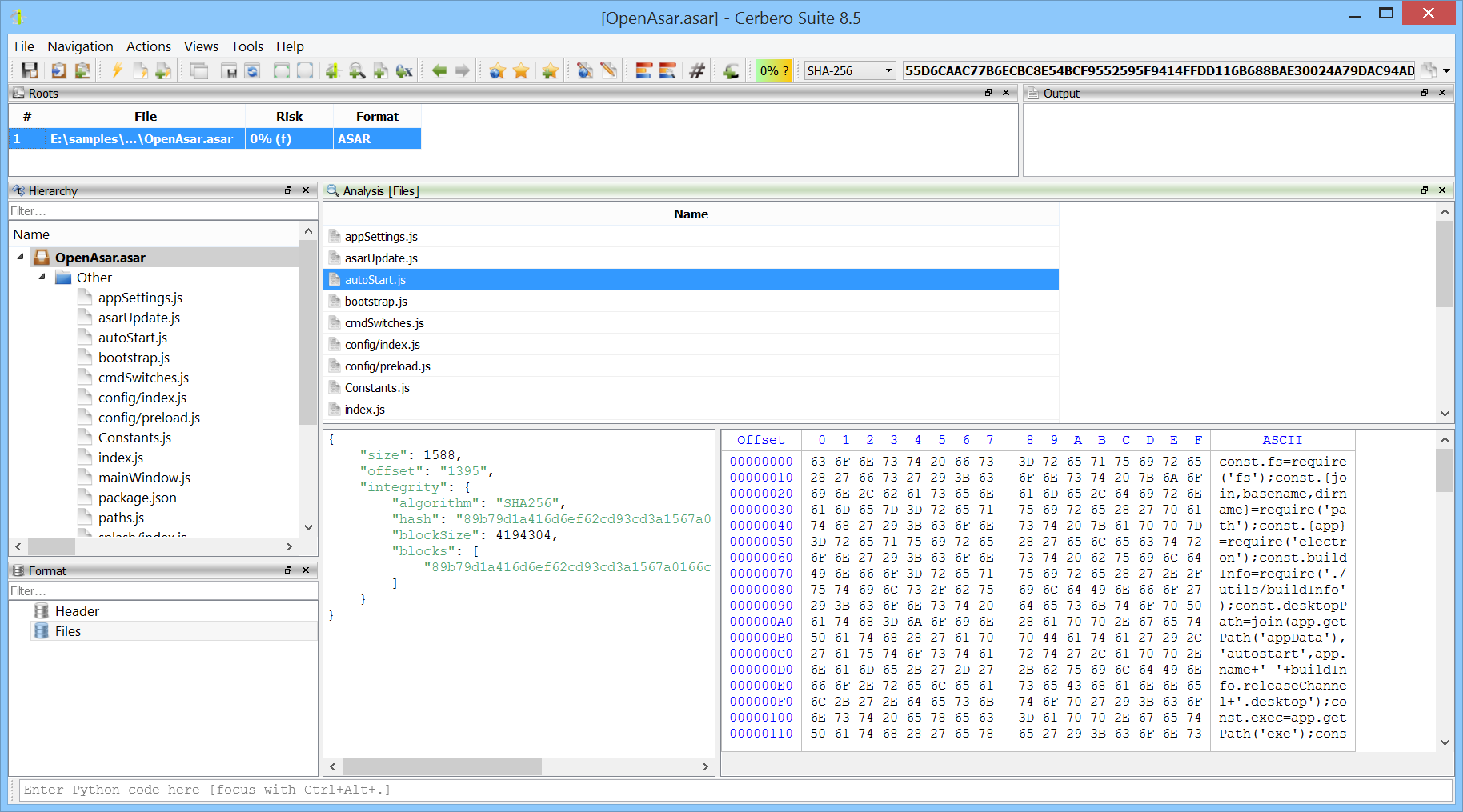
We’ve released the ASAR Format package, which adds support for the Atom Shell Archive Format, which is a lightweight archive format primarily used in Electron applications.
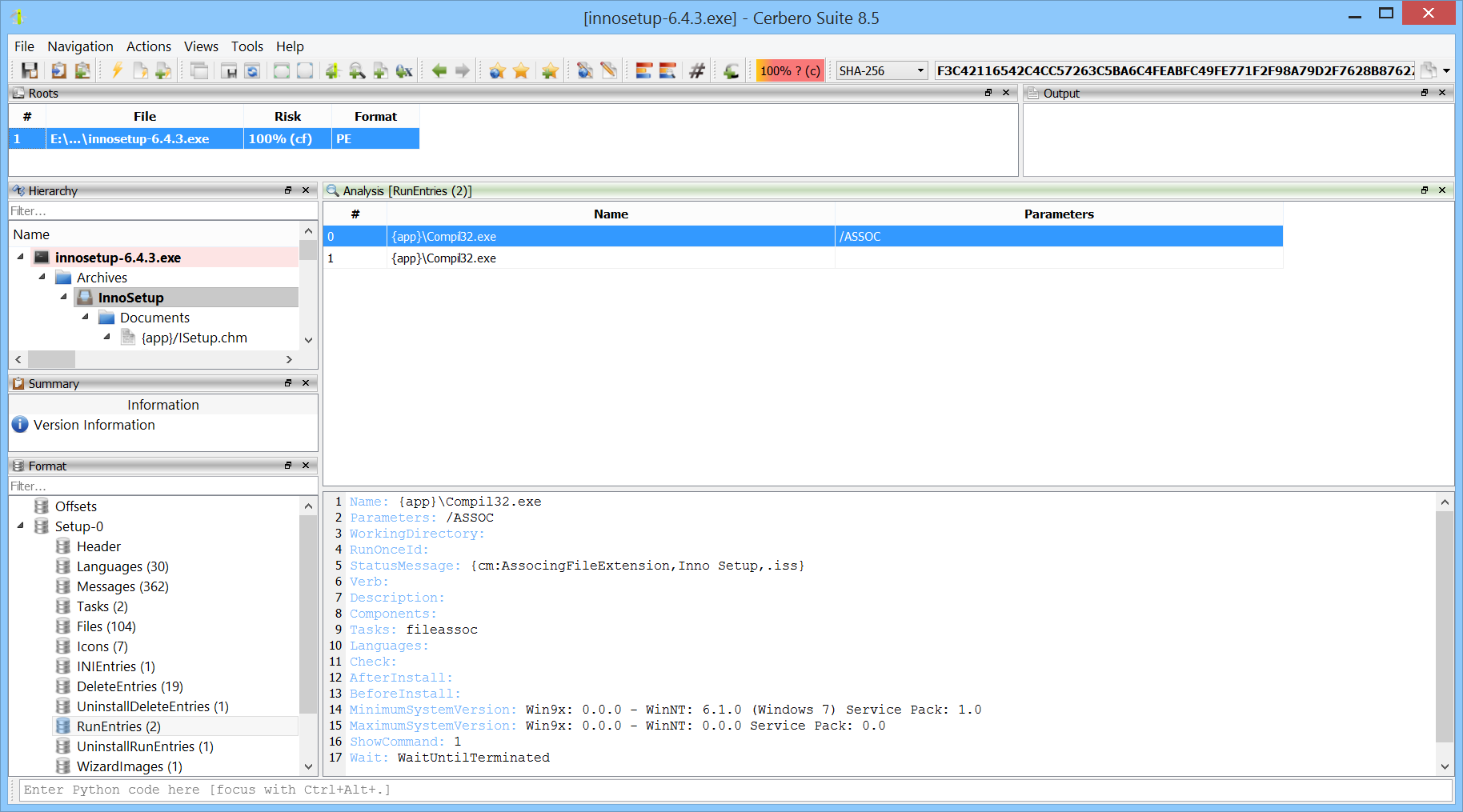
Version 2 of the InnoSetup Format package is now available and includes support for the latest releases of InnoSetup.
The 6th issue of Cerbero Journal, our company e-zine, is out! Since we’re late in releasing this journal, we decided to skip the usual early access for customers and make it available to everyone right away.
In this issue, we present the new Memory Analysis package alongside significant improvements such as file system support, customizable panels, and enhanced table features. We also cover topics ranging from paging and prototypes to UEFI firmware analysis, and include a hands-on memory dump challenge. To round it off, we’ve added a summer crossword puzzle.
We’ve released version 0.5 of the Memory Analysis package, currently in beta, and have also made it available to personal licenses of Cerbero Suite!
One of the cool features we worked on is hyperlinking processes and modules, allowing you to jump directly to a process or module analysis from any view. When opening a memory dump, you can choose to skip scanning processes and modules for faster inspection—yet still jump directly to a specific module and inspect it.
Why scan everything when you only need what matters? Apart from being able to skip scanning processes in a memory dump or scan all of them, we’ve added the capability to scan only processes of interest — making your analysis faster and more focused.
Modules and files can, as usual, be scanned using YARA. Additionally, the user-mode memory of processes can be scanned using our cutting-edge YARA Rules package.
User-mode memory can also be mined for files using our advanced File Miner package.
We’re continuing to expand the functionality of the Memory Analysis package with the goal of making it a state-of-the-art solution for memory forensic examiners. With each update, we’re adding powerful new features and refining the experience to support fast, focused, and in-depth analysis. More is on the way.
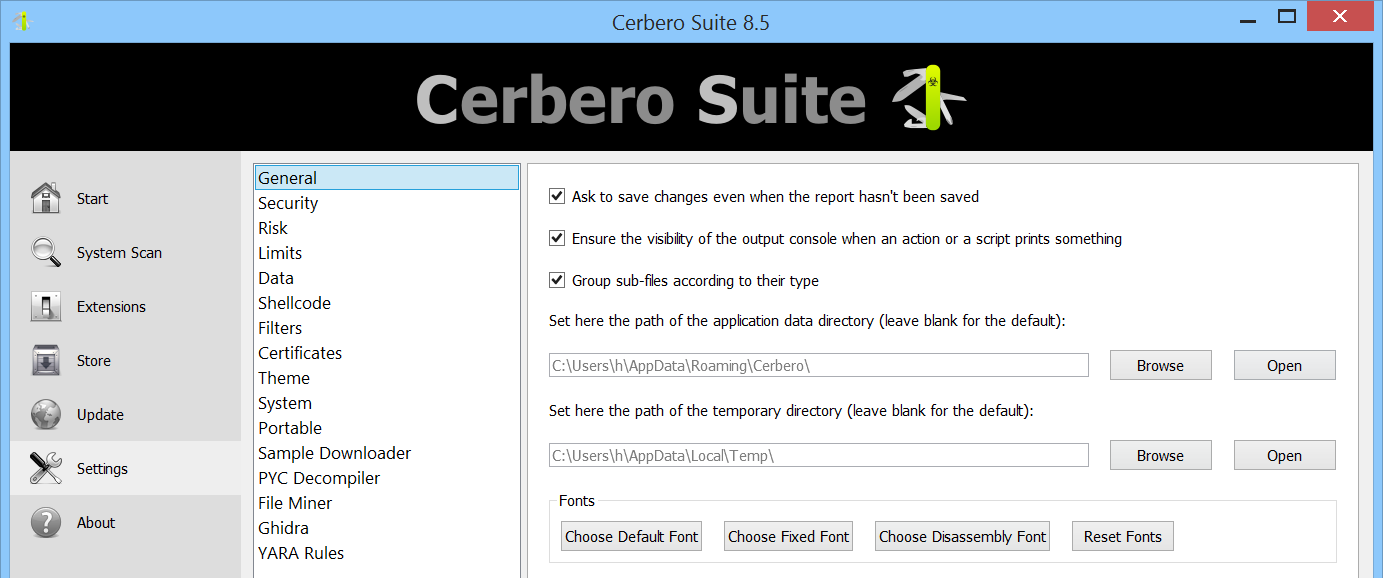
Cerbero Suite 8.5 and Cerbero Engine 5.5 are out! Most improvements are under the hood or related to the SDK.
One small but useful addition worth mentioning is the ability to configure a global font for the entire application.
We’ve released version 0.4 of the Memory Analysis package, currently in beta for our commercial customers and soon to be available for personal licenses too. The main highlight is that, thanks to Cerbero Suite 8.4, all tables now support sorting — but there are other new features as well, which we’ll cover in this blog post.
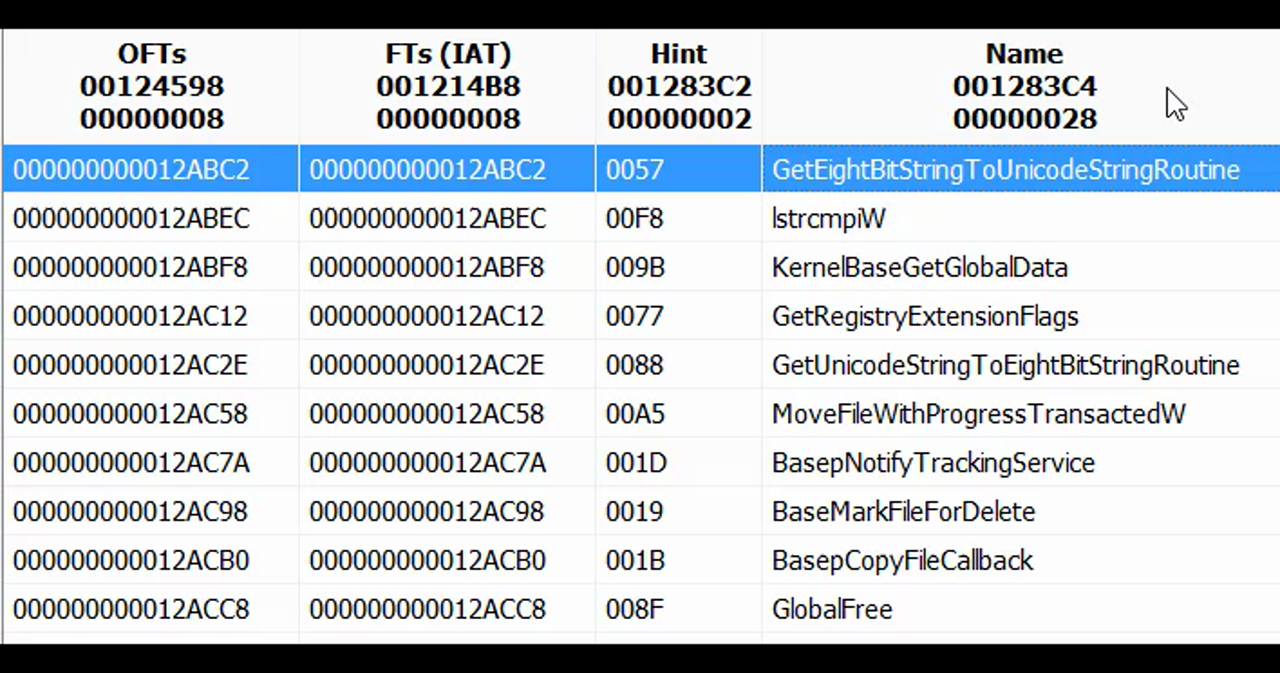
When inspecting a PE in memory, viewing the import table is useful — but seeing what the IAT entries actually point to is even better, especially if the import information is no longer available.
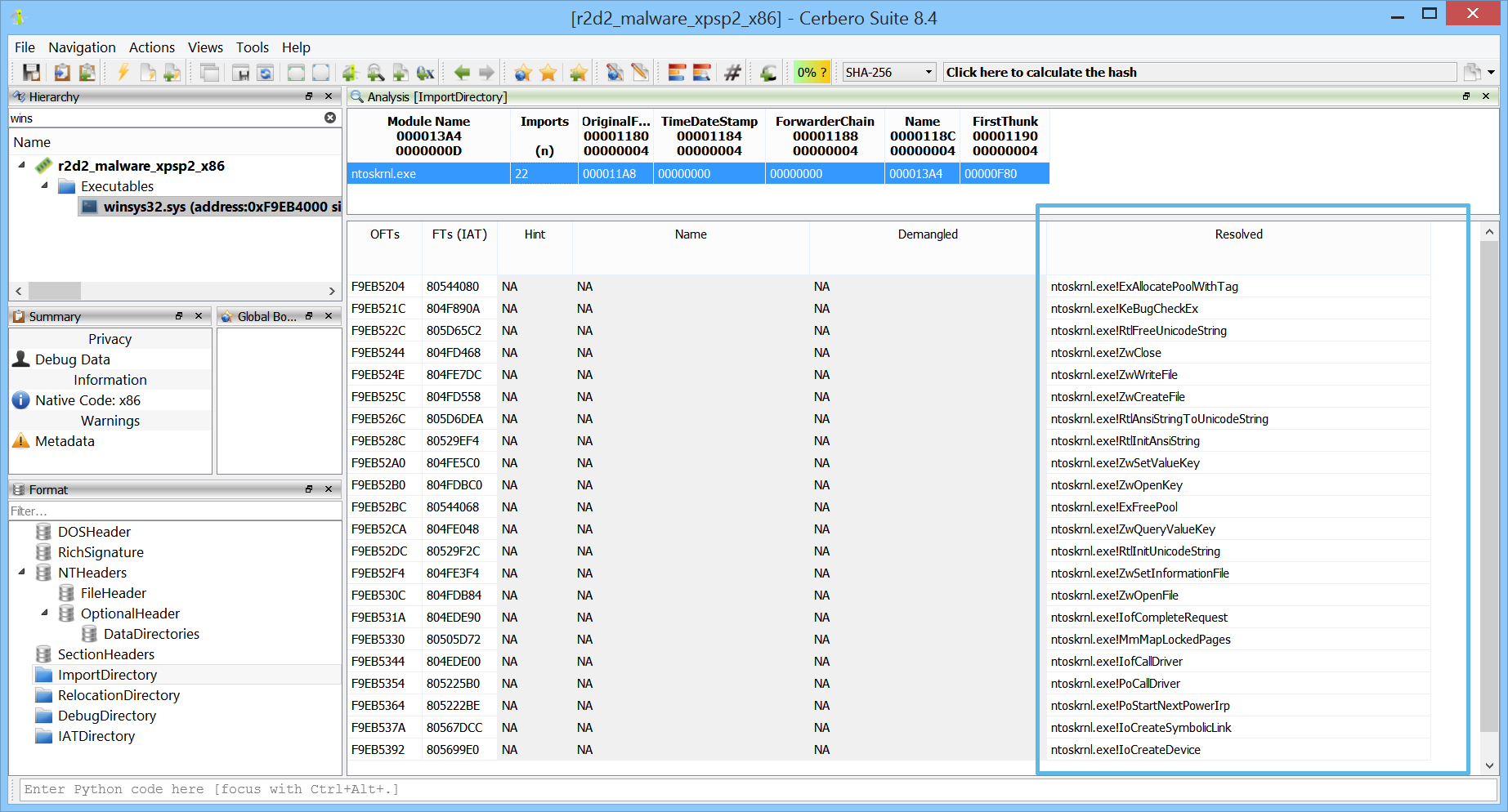
We’re happy to announce the release of Cerbero Suite 8.4 and Cerbero Engine 5.4. This might be a minor version, but we’ve added some important features that have been on our list for a while.
This has been a long time coming—most tables in Cerbero Suite can now be sorted. If a plugin uses the default table control, sorting works automatically without any extra effort.