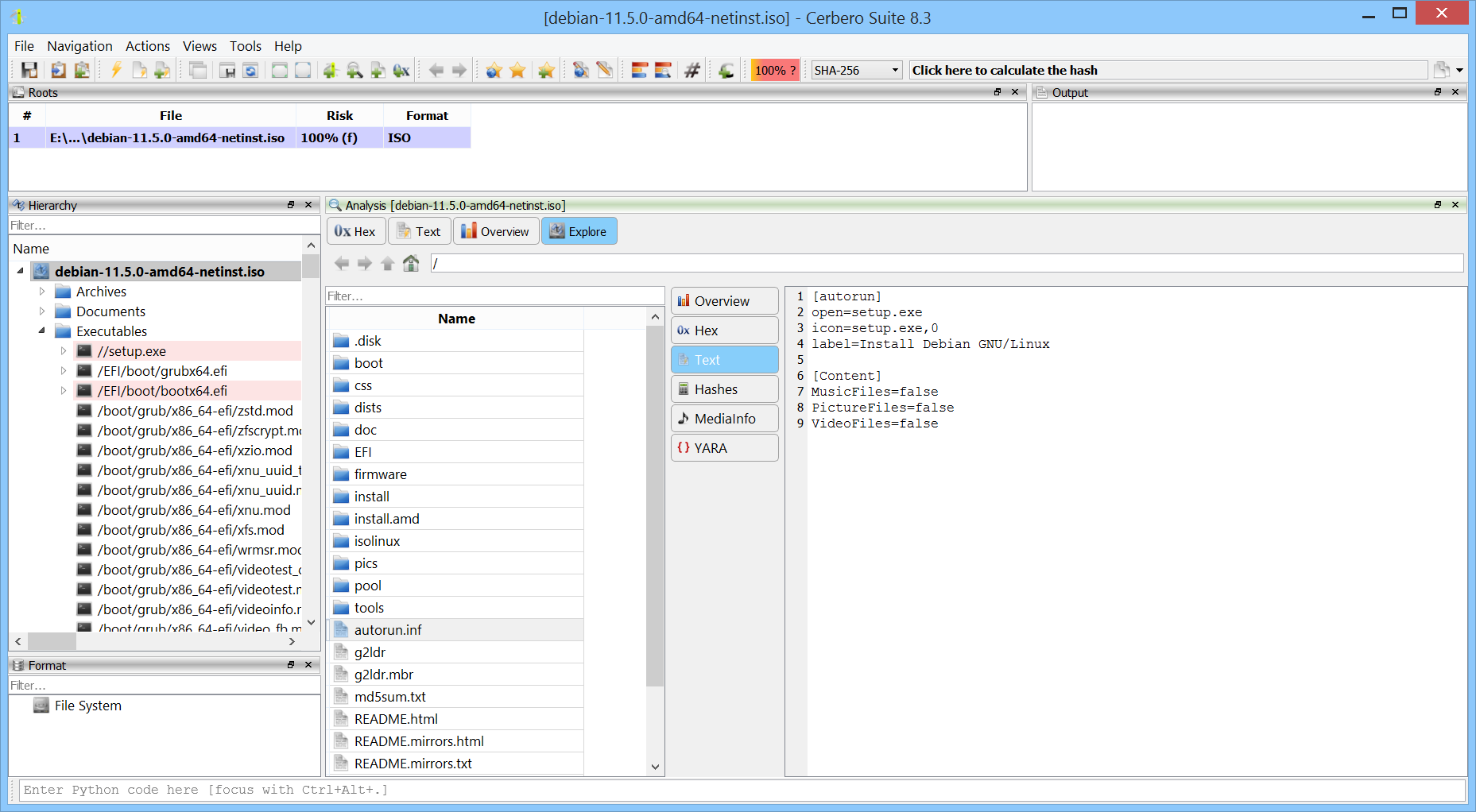
We’re excited to announce the release of the WIM Format package, which adds support for the Windows Imaging (WIM) file format.
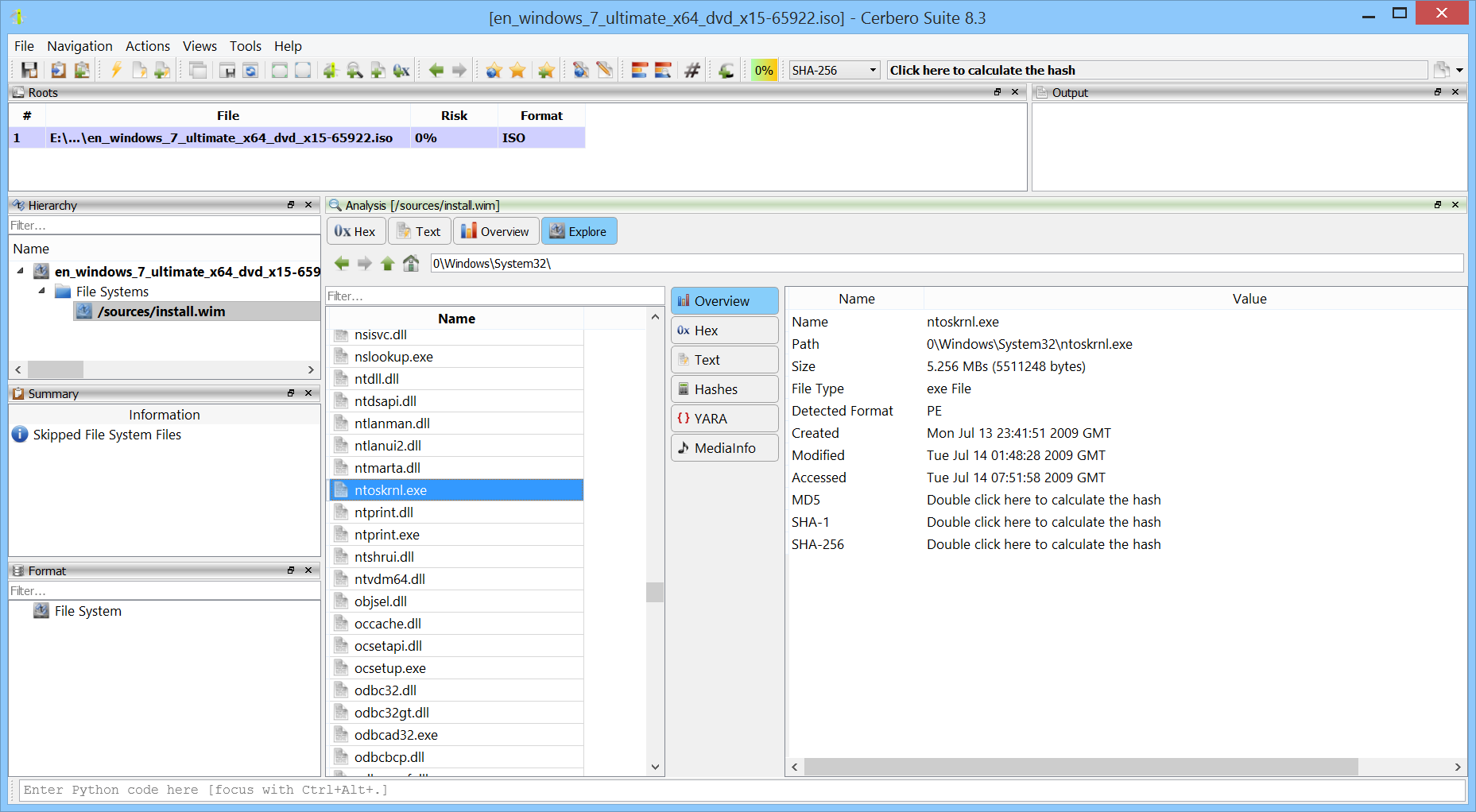
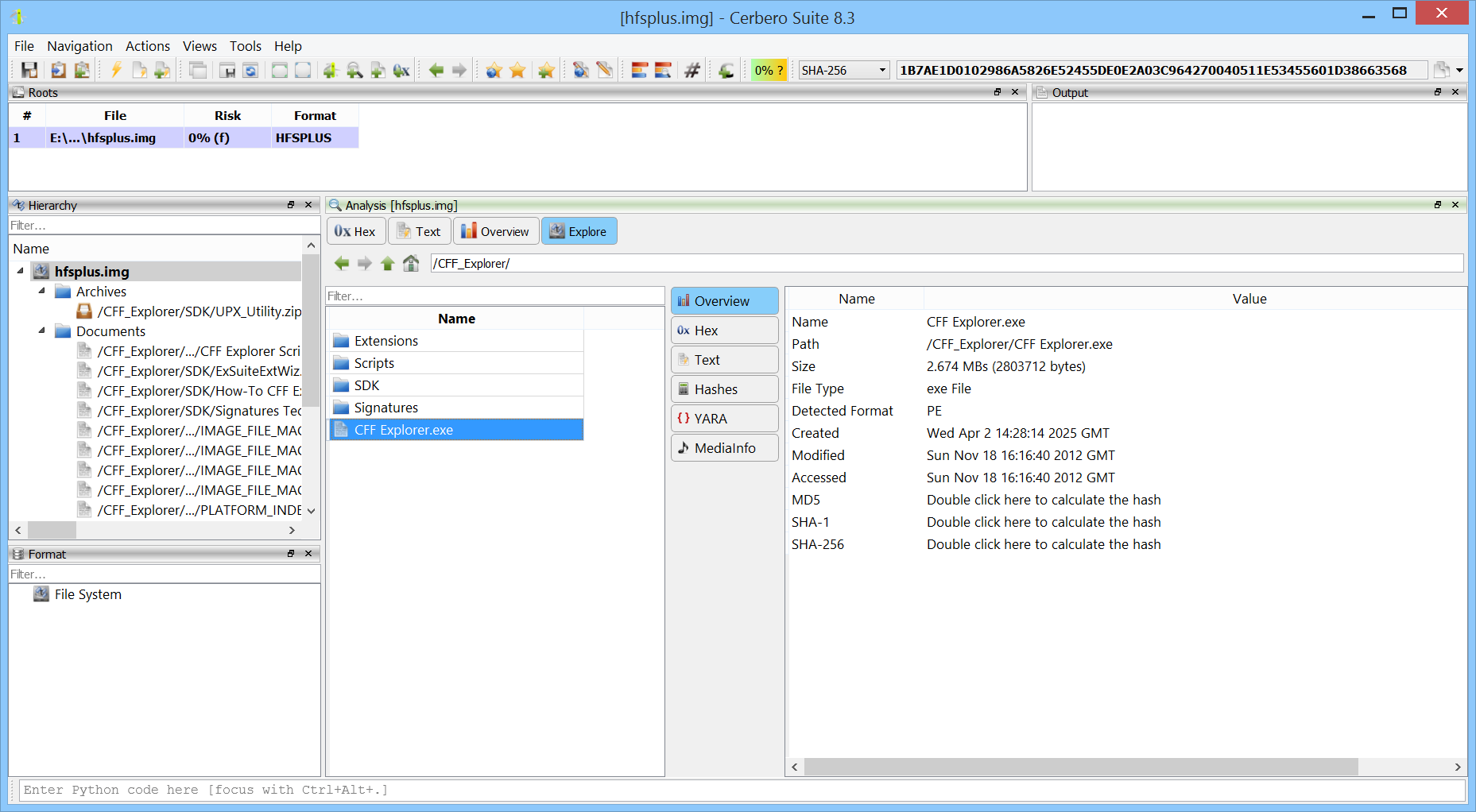
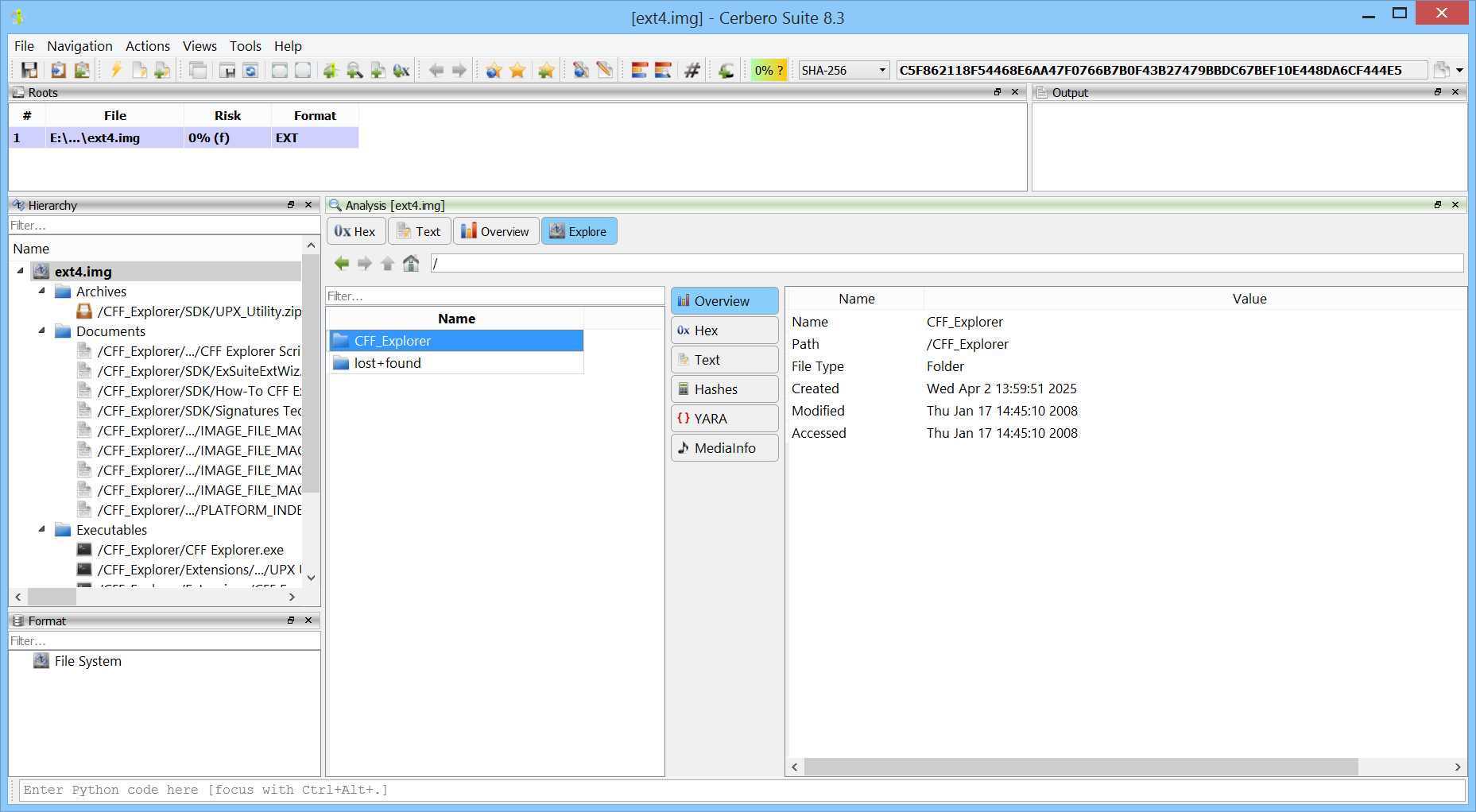
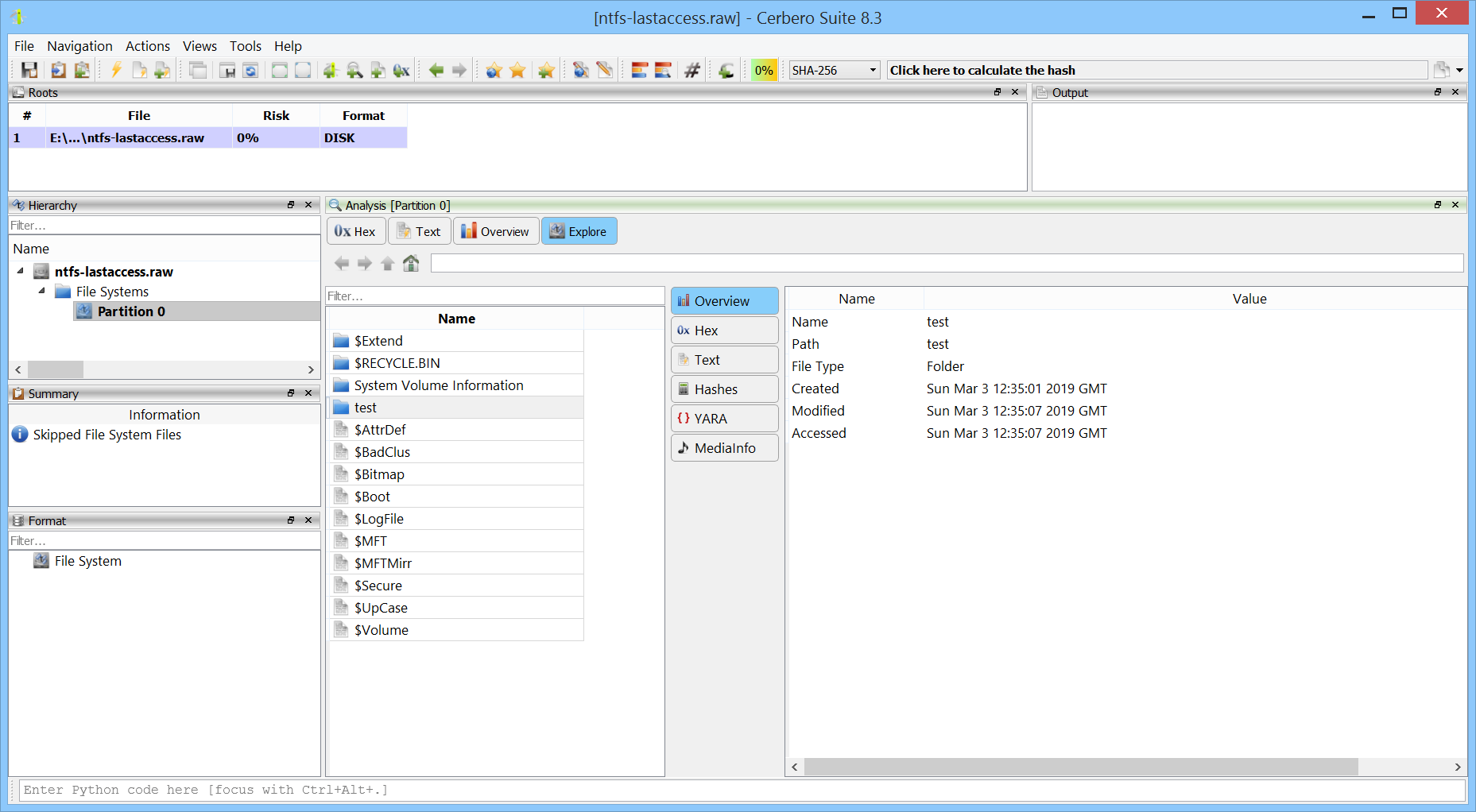
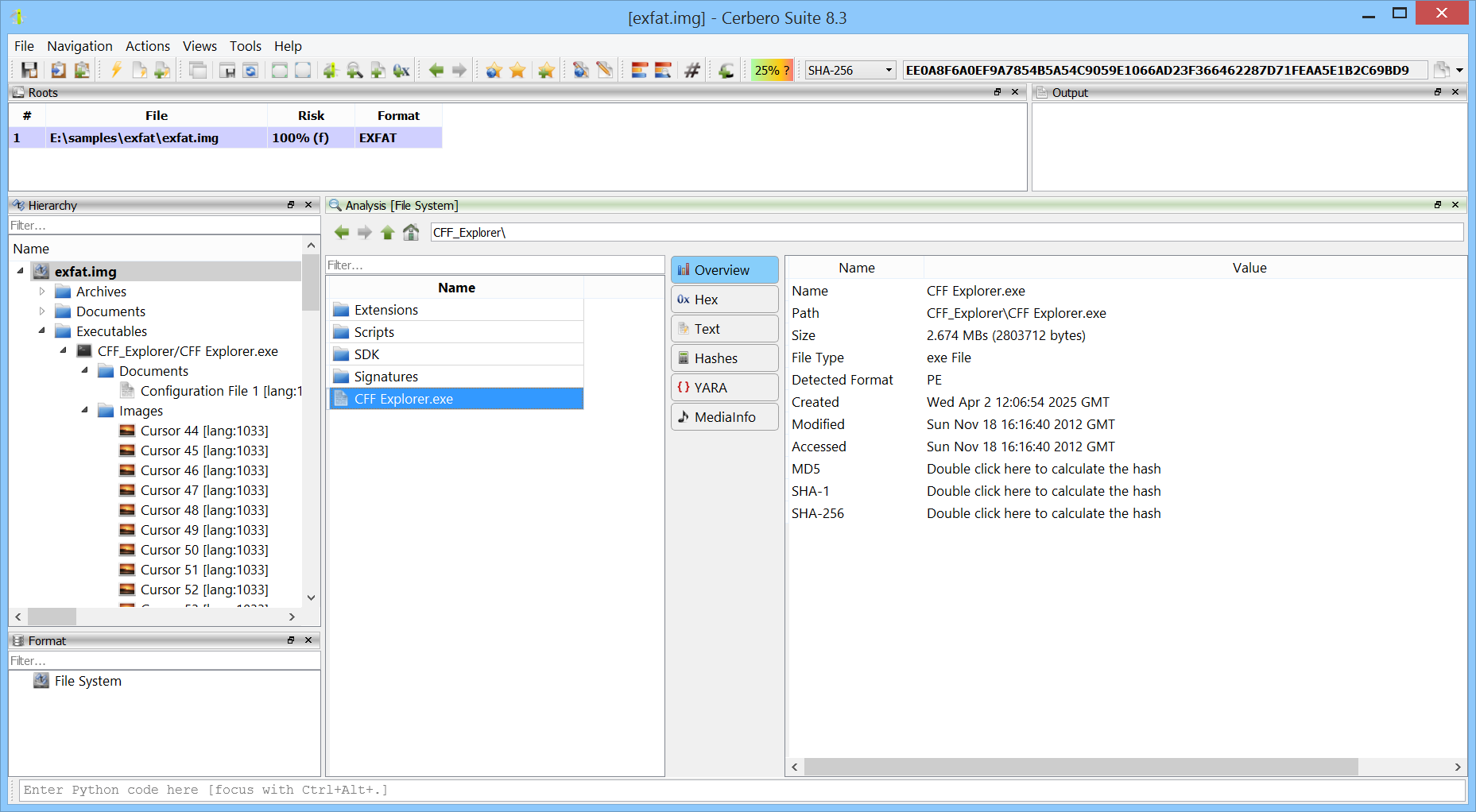
Once installed, you can explore the contents of WIM images directly in Cerbero Suite. This includes browsing the file hierarchy, inspecting individual files, and performing in-depth forensic analysis.
Additionally, when used in conjunction with the ISO Format package, it’s possible to seamlessly access WIM images embedded within ISO files—making the analysis of Windows installation media even more efficient.